适用于 IT/OT 的解决方案
在迅速融合的 IT/OT 世界中降低网络风险并保障运营安全
运营技术 (OT) 与 IT 系统的融合以及物联网技术的快速采用能够优化生产、推动创新并提升效率。但融合也可能扩大攻击面,并引入更多攻击载体。
申请演示
为工业运营和重要基础设施提供工业级的安全性
检测复杂且不断发展的网络威胁需要先进的工具、知识和培训。例如,OT 环境包含的远不止于 OT。多达半数 OT 环境中还可能包含基于 IT 的设备。阻止攻击和防止破坏需要能够同时应对这两大领域的专业能力和全方位安全措施。
有关被动融合的更多信息,请阅读本篇 IT/OT 安全运营指南。
全企业范围的可见性
无论您的企业是小型单一站点还是跨复杂、分布式环境的数百个站点,阻止攻击需要具备看到攻击的能力。在过去,孤立的 IT 和 OT 安全实践产生了严重的盲点,从而限制了检测漏洞和防止攻击的能力。包含 Tenable Nessus 的 Tenable OT Security 可消除盲点,并通过单一解决方案中的 IT 和 OT 领域专业知识,让您全面了解网络安全风险。通过 Tenable OT Security,企业可以全面识别潜在风险,并更快解决安全威胁。
Tenable OT Security 支持目前市场上 90% 以上的 PLC 产品,并能够与 Tenable 产品组合完全集成。为了充分利用现有的 IT 安全投资,Tenable OT Security 还能与业界领先的企业 IT 安全产品集成。 为此,我们打造出了一套全面的安全解决方案,能够利用所有安全产品,并提供前所未有的 IT 和 OT 可见性,帮助企业理解并防御整个攻击面。
下载 OT 环境的工业网络安全解决方案概要。
威胁检测和缓解
通过识别可能用于发起攻击或利用安全弱点的区域,从而主动发现 OT 环境中的弱点。通过将强大的网络和基于设备的威胁检测引擎结合使用可发现更多威胁,这些引擎对来自 IT 或 OT、外部和内部来源(无论是基于人为、勒索软件还是恶意软件)的潜在事件发出警报。
Tenable OT Security 能够识别异常的网络行为、执行网络安全策略和签名并追踪设备本地的变更,以便于企业检测并防范工业控制系统 (ICS) 环境中的风险活动。
通过精细调整策略、异常和特征,定制最适合企业运营的安全措施和警报。通过上下文感知警报和详细信息提供必要情报,全面、细致地了解所发生的事件,并在此基础上对威胁做出有意义的响应。
下载预测 OT 攻击白皮书。

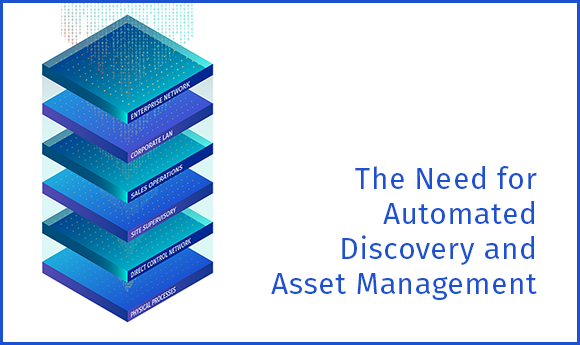
资产追踪
Tenable OT Security 的自动化资产发现和可视化能力提供了所有资产最全面、最实时的存量清单,包括工作站、服务器、人机界面 (HMI)、历史记录、可编程逻辑控制器 (PLC)、远程终端单元 (RTU)、智能电子设备 (IED) 和网络设备。
Tenable 取得专利的主动查询能力可以发现不通过网络通信的休眠设备。存量清单具备无与伦比的资产信息深度,包括追踪固件和 OS 版本、内部配置、修补程序级别和用户,以及 IT 和 OT 资产的序列号和底板配置。

精确查找漏洞
主动识别并修复漏洞,免遭攻击者利用。利用全面细致的资产追踪能力,Tenable OT Security 通过漏洞优先级评级 (VPR) 生成相关威胁的评级和分类列表。该评级基于环境中的特定设备,以及固件版本、相关 CVE、Tenable 专有研究、默认密码、开放端口、已安装的修补程序等多种参数。报告包含了详细洞见以及缓解建议。
深入了解预测优先级分析。
配置控制
Tenable OT Security 能够追踪恶意软件和用户通过网络或直接对设备执行的变更。Tenable OT Security 提供了设备配置随时间变化的完整历史记录,包括特定梯形逻辑段、诊断缓冲区、标签表等细分记录。 这使得管理员能够建立带有“上一个经过确认的良好状态”的备份快照,从而加快恢复并遵守业内法规。

充分利用 Tenable 的“信任生态系统”
充分发挥现有安全投资。Tenable OT Security 与 Tenable Security Center 和 Tenable Vulnerability Management 完全集成,可提供整个融合运营上的完全可见性、安全保障和控制功能。 Tenable OT Security 与 Tenable Identity Exposure 携手可以识别可能导致 OT 环境中的勒索软件攻击的 Active Directory 错误配置和威胁。Tenable OT Security 还可以与使用中的 IT 服务管理、新一代防火墙 (NGFW) 和安全信息以及事件管理 (SIEM) 供应商等 IT 安全技术进行全面集成。
通过与 Tenable 系列产品以及领先的 IT 和 OT 安全系统集成和协作,企业可以获得全面的态势感知,从而更好地保护运营免受当今的 IT 和 OT 威胁。
阅读 Tenable 解决方案在 OT 环境中的强大威力白皮书了解更多信息。