The First Major Security Logos of 2018: Spectre and Meltdown Vulnerabilities
This post was updated on Jan. 12, 2018 to include additional technical details and supplemental links.
The recently disclosed Meltdown and Spectre vulnerabilities started off 2018 with a somber note, as the attacks affect everything from desktops, laptops and mobile devices to cloud providers’ infrastructure. The flaws are present in nearly all modern microprocessors and can allow an attacker to access privileged memory by abusing a feature called speculative execution.
Speculative execution
Speculative execution is a technique that allows a microprocessor to increase performance by operating on multiple branches of instructions at once. To do this, the microprocessor predicts which branch of execution is most likely to be taken and starts executing that branch before it is reached. If this prediction ends up being incorrect, the microprocessor is designed to roll back the speculatively executed instructions in a way that is transparent to the software.
Both Meltdown and Spectre can abuse this feature to access privileged memory from a less privileged process. The differences are in which components of speculative execution they abuse and how they apply to different implementations. Google’s Project Zero blog discusses the issues in detail, but here’s a quick overview on how they work.
Meltdown
The Meltdown variant (#3 discussed in the GPZ blog) can allow a userspace attacker program to read privileged kernel memory. It exploits a race condition between the memory access and privilege checking while speculatively executing instructions. This occurs when unauthorized addresses are speculatively loaded into the microprocessor cache temporarily while the privilege checking is being performed at the same time. This attack gets much more complex and is explained in detail in the Meltdown whitepaper.
Spectre
The Spectre variants (#1 and #2 discussed in the GPZ blog) can allow an attacker controlled process to read arbitrary memory belonging to another process. This other process can be the kernel itself, but the key with Spectre is that it requires a specific attack tailored to the victim process. The way it works is that the attacker process first trains the branch predictor to expect a certain branch path will be taken. The attacker process then triggers execution of the victim process and times how long it takes to execute. Based on this timing, the attacker process can determine if the specific prediction that was trained was executed by the victim process or not. Again, this attack gets a lot more complex and is explained in detail in the Spectre whitepaper.
Affected microprocessors
Meltdown is an implementation-specific vulnerability and is known to affect Intel microprocessors. The good news here is that Meltdown can be patched via a microcode update. These microcode updates are distributed as both BIOS and operating system patches. Spectre, on the other hand, is a vulnerability in how branch prediction works in general and can affect any microprocessor with this speculative execution feature. When it comes to Spectre, there is no way to patch this vulnerability via microcode. However, most Spectre class vulnerabilities can be mitigated via software updates to your operating system or programs.
识别受影响的系统
Operating system vendors are forgoing regular patch release cycles and publishing operating system patches to address this issue. Tenable.io, SecurityCenter and Nessus can identify affected systems by looking for the newly released patches. Each plugin created for the Spectre and Meltdown vulnerabilities will be marked with at least one of the following CVEs :
- CVE-2017-5753: Systems with microprocessors utilizing speculative execution and branch prediction may allow unauthorized disclosure of information to an attacker with local user access via a side-channel analysis.
- CVE-2017-5715: Systems with microprocessors utilizing speculative execution and indirect branch prediction may allow unauthorized disclosure of information to an attacker with local user access via a side-channel analysis.
- CVE-2017-5754: Systems with microprocessors utilizing speculative execution and indirect branch prediction may allow unauthorized disclosure of information to an attacker with local user access via a side-channel analysis of the data cache.
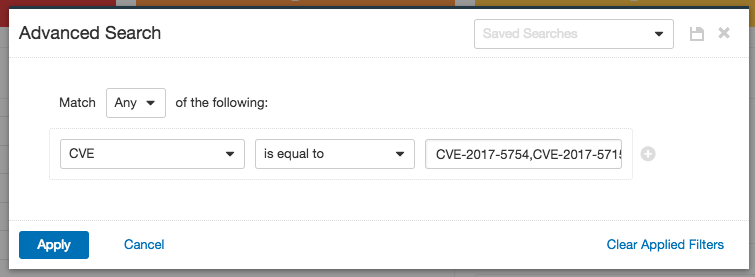
To identify which systems are affected using Tenable.io, open the workbench and, using the advanced search, apply a CVE filter (CVE-2017-5753,CVE-2017-5715,CVE-2017-5754) as shown below. In the example filter, each CVE is placed in the field separated using a comma.
个插件
When searching for the plugins using CVE you will find several plugins. Please note, as new plugins are available they will be automatically added to the plugin feed.
| 爱达荷州 | 名称 |
|---|
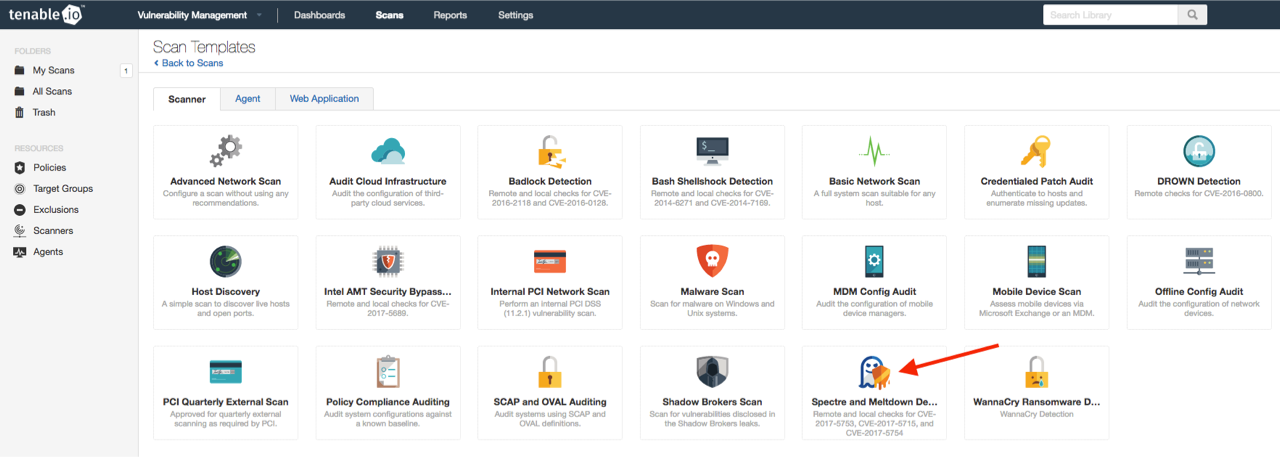
Scanning for vulnerabilities
Tenable.io and SecurityCenter users will receive a new scan policy to run scans targeting Spectre and Meltdown. To create a scan job, go to ‘Scan policy templates’ and select the policy shown in the image below. All of the required plugins are assigned to the policy. You will then need to add credentials for the systems you are targeting. All plugins in the policy require credentials to be executed.
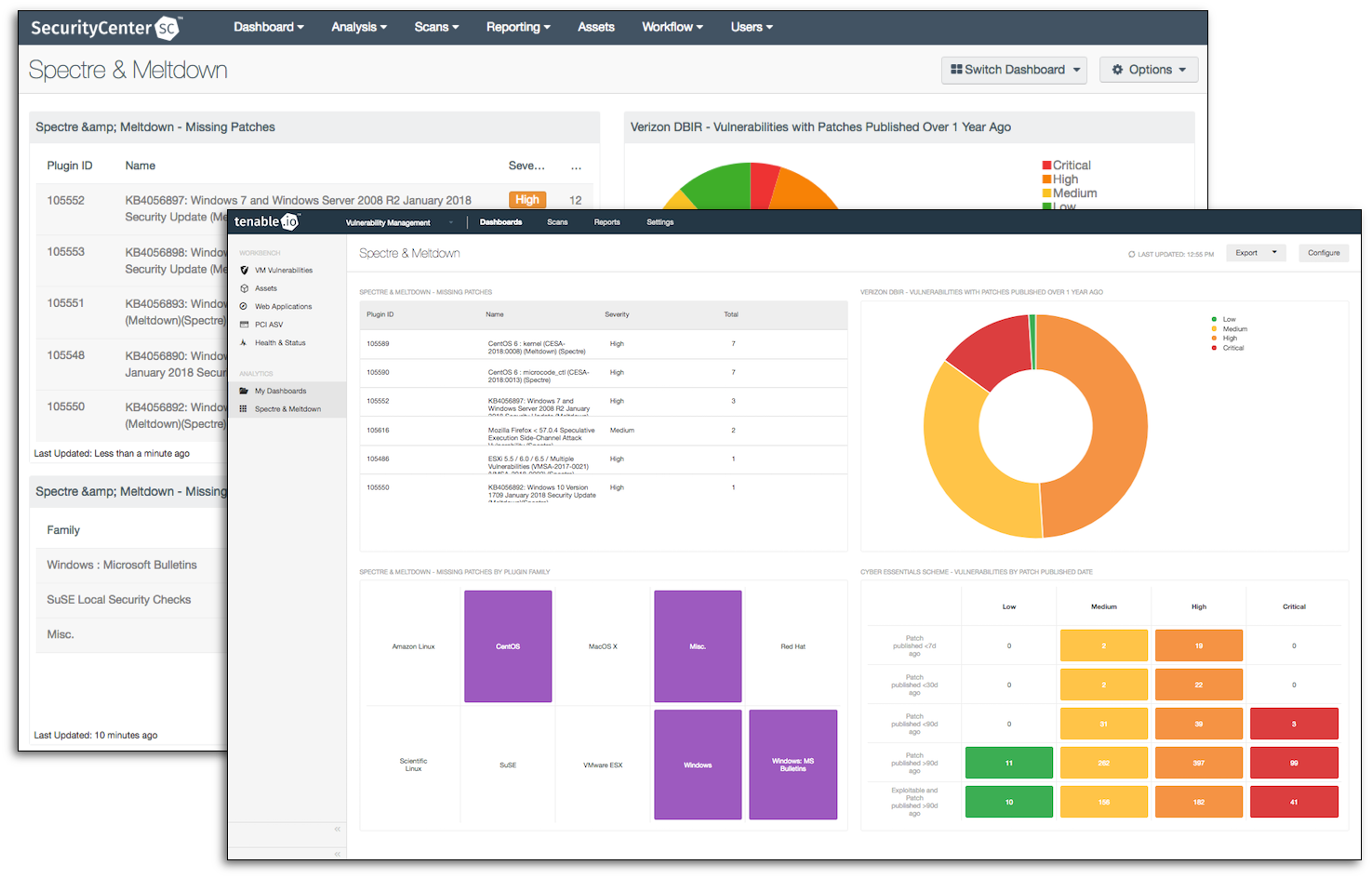
Dashboard
Tenable.io and SecurityCenter users can use the dashboard that's available in the feed allowing for easy identification of affected systems. The dashboard provides two components that use the CVE to group affected systems by Plugin Group and Vulnerability. Each view provides customers with a focused view of systems that need to be patched. The other components show how the customer is progressing with mitigating vulnerabilities based on patch published date.
Wrapping up
We will continue to research these vulnerabilities, and investigate different ways to detect them. When new information is available, we will release additional plugins. This vulnerability is a real and present danger to all organizations and should be patched immediately. While Microsoft, Red Hat, VMWare and other vendors are making efforts to release patches, organizations are responsible for applying those patches as soon as possible.
相关文章
- Nessus
- Plugins
- SecurityCenter
- Tenable.io
- Vulnerability Management