New Apache Struts Vulnerability Could Allow for Remote Code Execution

Updated August 23: A working proof of concept (PoC) has been discovered and verified on Github by Tenable’s research team. In addition, there are indications that attackers are already probing for vulnerable Apache Struts instances.
背景
Semmle researchers discovered and disclosed a remote code execution (RCE) vulnerability (CVE-2018-11776) in servers running Apache Struts that meet specific configuration requirements. According to Semmle, those requirements are:
- The alwaysSelectFullNamespace flag is set to true in the Struts configuration. (Note: this is automatically the case if your application uses the popular Struts Convention plugin.)
- The application’s Struts configuration file contains an <action ...> tag that does not specify the optional namespace attribute or specifies a wildcard namespace (e.g., “/*”).
This vulnerability also requires the version of Apache Struts to be Struts 2.3–Struts 2.3.34 or Struts 2.5–Struts 2.5.16. Upgrading to the latest version provided by Apache should mitigate your risk.
Impact assessment
If the above configuration requirements are met and your version of Apache Struts has not been updated to the recommended versions, then an attacker could take full control of the web application using Apache Struts.
Equifax saw a similar Apache Struts vulnerability (CVE-2017-5638) used in what has been called the most expensive data breach in history. Many web-based RCE vulnerabilities like this one are researched quickly, with publicly available exploits appearing in less than a few days after disclosure. In fact, our recent Attacker's Advantage report found that 34 percent of the most prevalent vulnerabilities had an exploit available on the same day they were disclosed.
Vulnerability details
In Apache Struts, when the <action ...> tag doesn’t have a corresponding namespace attribute, the default redirectAction result type will pass unsanitized strings in an HTML request as commands.
In addition, <s:url …> tags without a preset action or value attribute can be manipulated by having malicious code injected into the missing attributes, which then get passed to Struts as executed commands.
Urgently required actions
Upgrade to Apache Struts version 2.3.35 or 2.5.17 as soon as possible.
Apache also states that the following configuration change can mitigate the vulnerability (this should be a temporary workaround until an organization can upgrade):
- Verify that you have a set namespace (if applicable) for your ‘all’ defined results in underlying configurations.
- Verify that you have a set value or action for all ‘url’ tags in your JSPs. Both are needed only when their upper action(s) configurations have no or wildcard namespace.
Researchers at Semmle have suggested that other methods of attack could exist, and these configuration requirements may not prevent attack.
Identifying affected systems (Updated August 24)
Unauthenticated Remote Check
Plugin 112064 is a remote plugin which will attempt to exploit the vulnerability and send an ICMP echo (ping) request from the remote host back to the scanner host to verify a successful exploit.
Enabling a proper scan test requires the following steps:
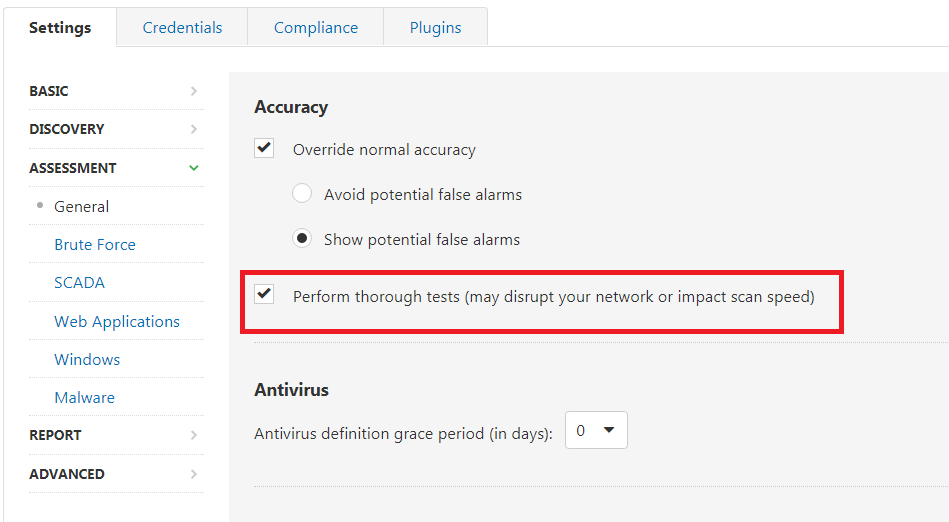
- First, enable the scanner to “perform thorough tests” under the Assessment -> General Settings.
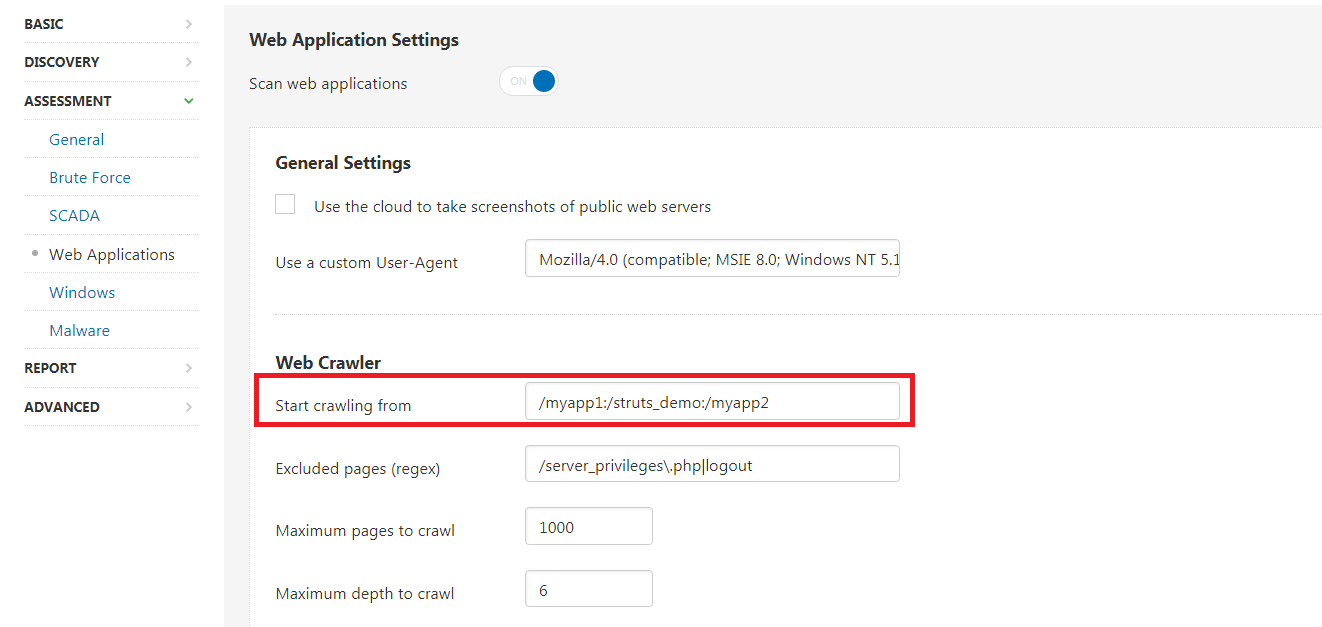
- Second, enable a Web Application Scan in Assessment Settings. Be sure to configure the scan with the appropriate location to start crawling the web application. In the Web Applications section of Assessment Settings, define the “Start crawling from” location for the Web Crawler as highlighted in the image below.
- Finally, for highly segmented and compartmentalized networks, it is important for the target to have the ability to ping the scanner’s direct IP. This is especially important in cloud environments where VPCs, subnets, and containerized applications can interfere with the communication the plugin sends from the target to the scanner to verify that the blind remote code execution vulnerability exists.
注:This plugin will not work from Tenable.io scanner pools due to the nature of the vulnerability. Customers are encouraged to run the scan with their own on-prem scanners.
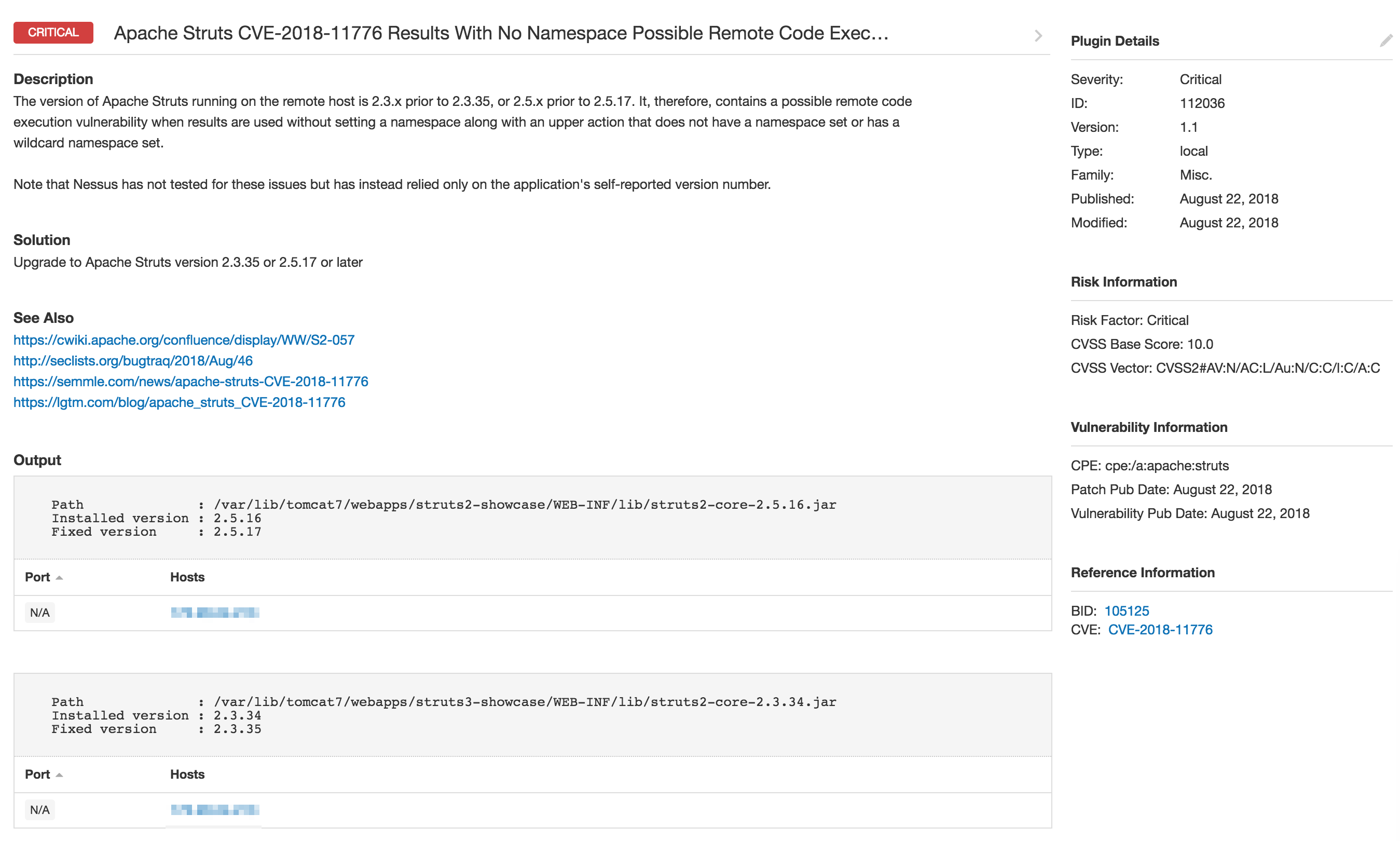
Authenticated Local Check
Plugin ID 112036 is available for both Windows (using SMB credentials) and Unix (using SSH credentials). Note that this plugin only runs in scans where the Accuracy setting is set to Show potential false alarms. Since the plugin relies only on the version number identified for a Struts application, this plugin is unable to identify if a workaround is in place which mitigates the vulnerability. For this reason, the Accuracy setting must be set to Show Potential false alarms.
Tenable.io Container Security can detect containers running versions of Apache Struts that are vulnerable to CVE-2018-11776.
Important Note: Apache suggests that older unsupported versions of Struts may be vulnerable as well, and recommends upgrading to the latest versions to be secure.
|
Plugin ID |
Description |
|
Apache Struts CVE-2018-11776 Results With No Namespace Possible Remote Code Execution (S2-057) |
|
|
Apache Struts CVE-2018-11776 Results With No Namespace Possible Remote Code Execution (S2-057) (Remote Check) |
Example plugin output for an affected system can be seen below:
获取更多信息
- Semmle's public disclosure
- Researcher Man Yue Mo's technical explanation of the vulnerability
- Apache's advisory
- NVD entry for CVE-2018-11776
Learn more about Tenable.io, the first Cyber Exposure platform for holistic management of your modern attack surface. Start your free trial of Tenable.io Container Security now!
相关文章
- Tenable.io Container Security







