Microsoft 2019 年 7 月星期二补丁:您需要了解的要点

Microsoft’s July 2019 Security Updates were released on July 9, with nearly 80 vulnerabilities patched in this update, 15 of which are critical.
CVE-2019-0865 | SymCrypt Denial of Service Vulnerability
A denial of service vulnerability was identified in SymCrypt, the cryptographic library used to handle cryptographic functions on Windows. Using a specially crafted digital signature, an attacker could exploit this flaw by embedding the signature in a message or as part of a secure connection request. This vulnerability was publicly disclosed in June by Google Project Zero researcher Tavis Ormandy.
CVE-2019-0785 | Windows DHCP Server Remote Code Execution Vulnerability
A memory corruption vulnerability in the Windows Server Dynamic Host Configuration Protocol (DHCP) service could allow a remote malicious attacker to run arbitrary code on a DHCP failover server, or perform a denial of service (DoS) attack. An attacker would need to send a malicious DHCP request to the DHCP server, but the server must be set to failover mode.
CVE-2019-1132 | Win32k Elevation of Privilege Vulnerability
An elevation of privilege vulnerability that enables improper handling of objects in memory by a Win32k component could result in arbitrary code execution in kernel mode, which is typically reserved for trusted functions of the operating system. An attacker would first need to establish a presence on a target system in order to exploit this vulnerability and gain elevated privileges.
CVE-2019-1102 | GDI+ Remote Code Execution Vulnerability
A remote code execution vulnerability exists in the way that the Windows Graphics Device Interface (GDI) handles objects in memory. An attacker who successfully exploited this vulnerability could take control of the affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
CVE-2019-0880 | Microsoft splwow64 Elevation of Privilege Vulnerability
An elevation of privilege vulnerability identified in splwow64.exe could be combined with a remote code execution or a separate elevation of privilege vulnerability to gain arbitrary code execution. Because it was exploited in the wild, it is likely that it was paired with another vulnerability, but those details are not currently available.
CVE-2019-0887 | Remote Desktop Services Remote Code Execution Vulnerability
A remote code execution vulnerability was identified in Remote Desktop Services. Exploitation of this vulnerability could result in arbitrary code execution, but requires an attacker to have already compromised a target system. This vulnerability was first published in a blog on Reverse RDP attacks in February 2019 which included one CVE that did not receive a CVE-ID.
CVE-2019-1130 | Windows Elevation of Privilege Vulnerability
An elevation of privilege vulnerability in Windows AppX Deployment Service (AppXSVC) due to improper handling of hard links. This patch follows CVE-2019-1064, another elevation of privilege vulnerability in AppXSVC that was publicly disclosed by researcher SandboxEscaper as a bypass of CVE-2019-0841 and addressed in the June 2019 Patch Tuesday release. CVE-2019-1130 is credited to Polar Bear, which is a reference to SandboxEscaper.
Tenable 解决方案
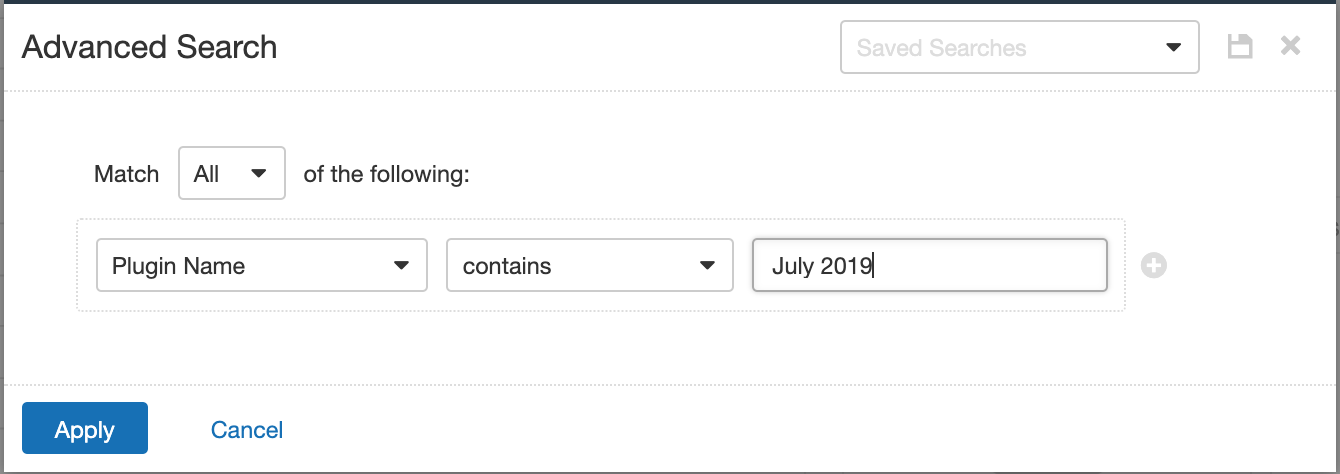
Users can create scans that focus specifically on our Patch Tuesday plugins. From a new advanced scan, in the plugins tab, set an advanced filter for Plugin Name Contains July 2019.
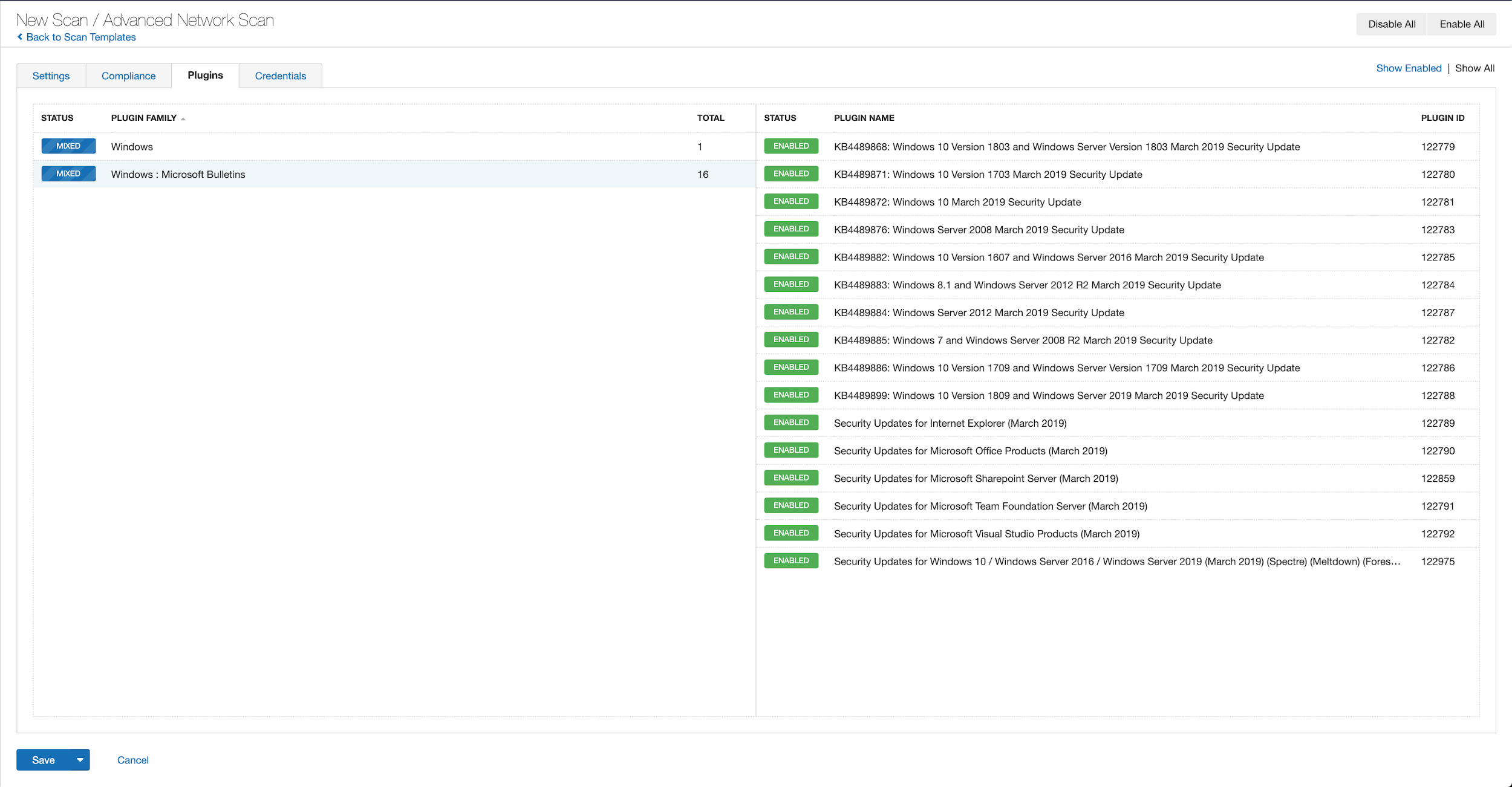
With that filter set, click on the plugin families to the left, and enable each plugin that appears on the right side. Note that if your families on the left say Enabled then that means all of the plugins in that family are set. Disable the whole family before selecting the individual plugins for this scan. Here’s an example from Tenable.io:
A list of all of the plugins released for Tenable’s July 2019 Patch Tuesday update can be found here.
了解详情:
相关文章
- Threat Intelligence
- Threat Management
- Vulnerability Management
- Vulnerability Scanning








