深入洞悉运营技术环境

Award-winning Tenable® Industrial Security adds approximately 350 new operational technology (OT) asset detections and delivers interactive 2D topology mapping and 3D visualization.
Tenable Industrial Security provides safe, reliable asset discovery and vulnerability detection purpose-built for industrial control systems (ICSs) and supervisory control and data acquisition (SCADA) systems. Based on Nessus Network Monitor, Tenable Industrial Security uses passive network monitoring designed for critical systems that require a non-intrusive approach to vulnerability detection. The OT-native solution helps identify and prioritize OT risks, so you can keep safety-critical production assets secure and fully functional.
To build on our strategic partnership with Siemens and expand visibility into industrial environments, we’re adding approximately 350 new ICS/OT asset detections. Nessus Network Monitor 5.5 achieved general availability on May 15 and adds approximately 150 new detections focused primarily on Siemens’ programmable logic controllers (PLCs) and human-machine interface (HMI) applications, including:
- 8 families of Siemens PLCs
- 3 families of Siemens HMIs
- 9 families of Siemens industrial drives
- 7 families of communications modules
Nessus Network Monitor 5.5.1 achieved general availability in June, adding approximately 200 new OT asset detections, including:
- 8 families of Schneider PLCs
- 2 families of Schneider HMIs
- 2 Schneider applications
- 2 families of Rockwell/Allen-Bradley PLCs
- 20+ new Modbus communications, drives, energy meters and other devices
The new asset detection capabilities are premium Nessus Network Monitor content, available when Nessus Network Monitor is used as a sensor for Industrial Security.
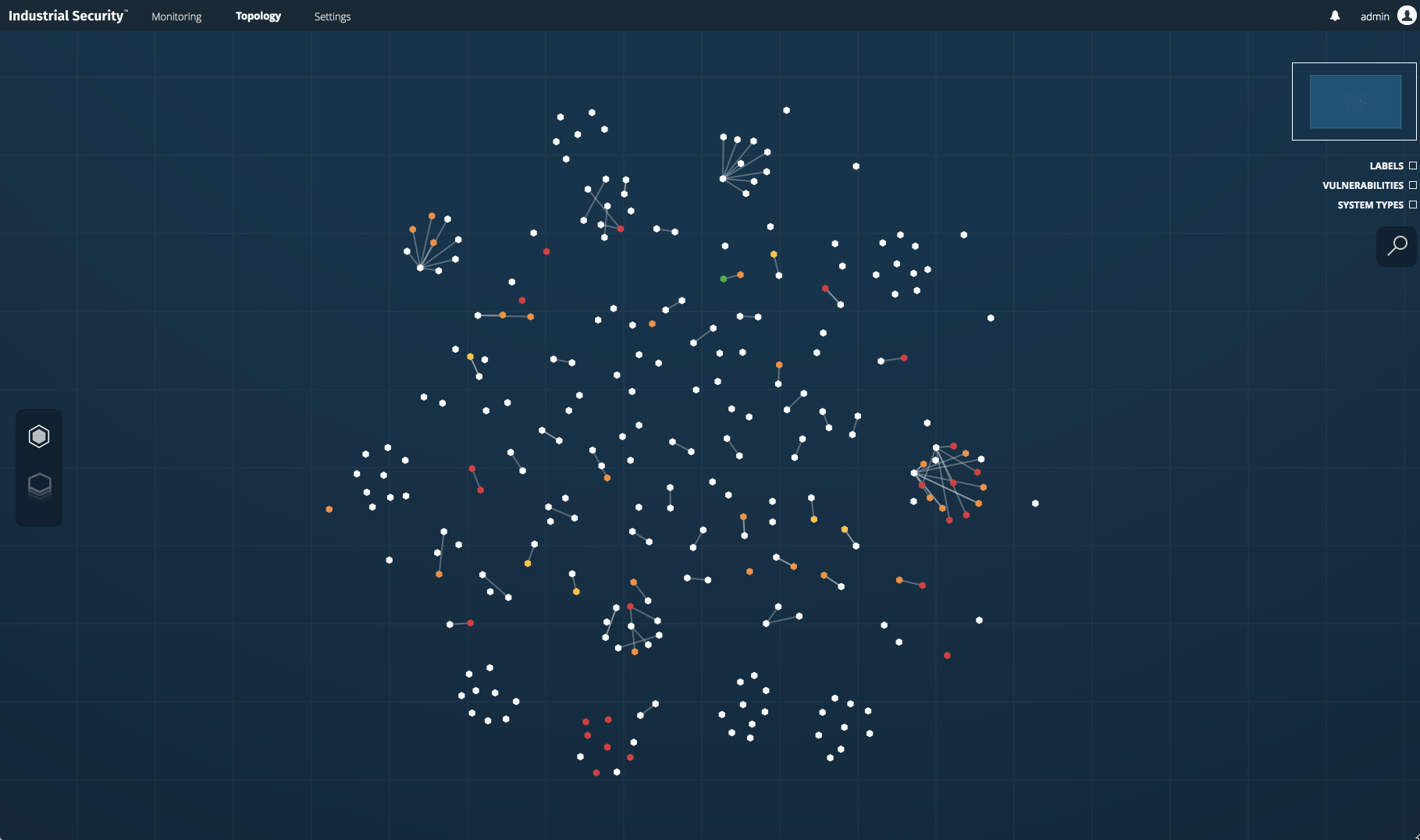
Interactive 2D topology mapping and 3D visualization – understand your OT environment in seconds
In addition to increased device support, Industrial Security 1.1, which also achieved general availability on May 15, has a significantly improved user interface with the addition of interactive 2D topology mapping and 3D visualization. With interactive topology mapping, you can understand your OT environment at a glance. Devices are clustered based on IP addresses, and vulnerabilities are color-coded to provide a cyber risk heat map.
Vulnerability insight is critical in OT environments
Understanding vulnerabilities in OT environments is a critical part of measuring and managing cyber risk. Patches are infrequently applied to ICS devices in the OT environment due to extremely high-availability requirements. Nonetheless, vulnerability insight is required to inform other mitigation strategies, such as stronger access controls, more restrictive firewall rules and data diodes (hardware that enforces one-way data flow). Visualizing and interacting with the plethora of information easily is necessary to gain the insights required to manage risk – which the new user interface delivers.
Use case: Determining where the business is most exposed
Consider this use case: You need to identify sections of your network where there may be increased risk. You use the vulnerability severity lens to see where your network has a large number of highly vulnerable assets communicating with one another. The following screen shots walk through that use case.
The screenshot below shows 225 monitored assets, clustered by connections. The color-coding shows vulnerabilities in a heat map:
- Red dots indicate critical vulnerabilities
- Orange dots indicate high vulnerabilities
- Yellow dots indicate medium vulnerabilities
- Green dots indicate information-level vulnerabilities
The screenshot below zooms in on the the most vulnerabilities. The icons represent the system type, the color-coding corresponds to the highest vulnerability severity level found on the device and the number represents the number of the most critical vulnerabilities.
![]()
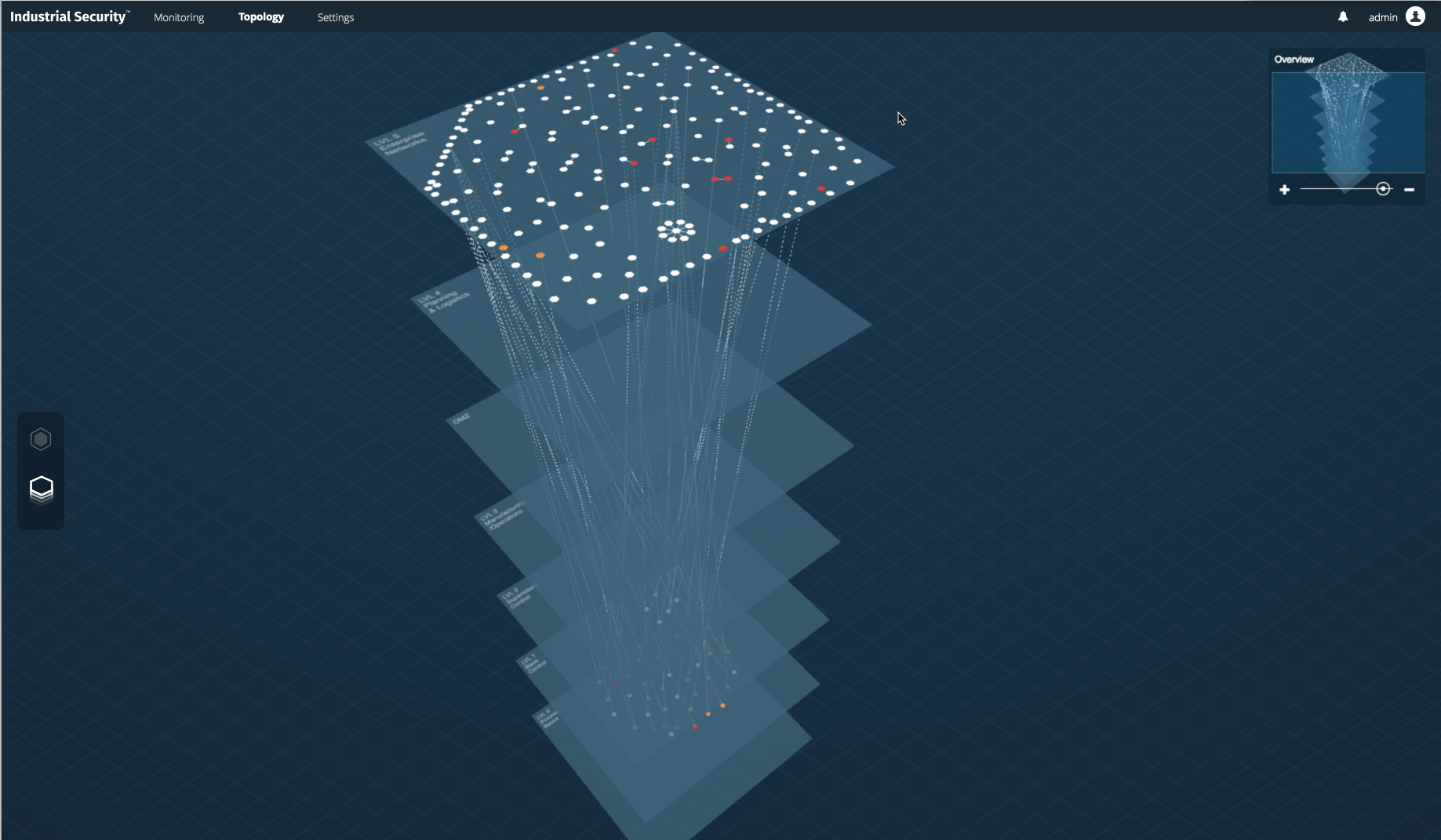
The 3D topology view shown below helps you understand connections across the Purdue Model.
The latest Nessus Network Monitor and Industrial Security releases give you greater insight into your OT environment, so you can better measure and manage cyber risk. To see Industrial Security in action, watch the on-demand webinar, Understand and Reduce Cyber Risk in Converged IT/OT Environments.
相关文章
- Energy Industry
- SCADA
- Vulnerability Scanning








