網路安全快照: Salary Trends, Ransomware Summit, Next-gen MFA

Get the latest on salary trends for CISOs and cybersecurity pros; CISA’s call for adopting phishing-resistant MFA; the White House’s ransomware summit; and more!
Dive into 6 things that are top of mind for the week ending Nov. 4.
1 – CISOs to employers: Show me the money!
Compensation for CISOs in the U.S. and Canada improved this year compared with 2021 as employers paid up to retain their cybersecurity chiefs amidst a shortage of qualified candidates for these jobs.
That’s according to the “2022 CISO Compensation Benchmark Report” from IANS Research and Artico Search, which polled more than 500 CISOs and found that total compensation went up 15% compared with last year to $495,000.
How challenging is it for organizations to hold on to their CISOs right now? Forty-two percent of respondents said they were actively mulling switching jobs in the next 12 months, while another 24% said they “might,” according to a companion blog post about the study.
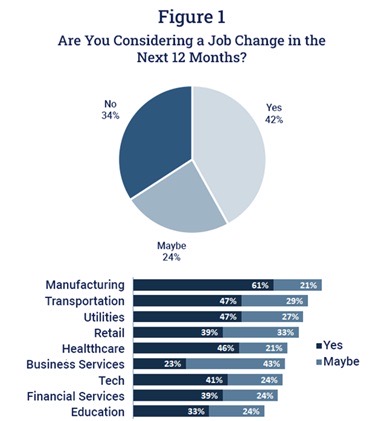
(Source: “2022 CISO Compensation Benchmark Report” from IANS Research and Artico Search, October 2022)
And who can blame CISOs for looking at greener pastures? The report found that respondents who switched jobs got on average a 37% bump in total compensation – salary, equity grants and bonuses – while those who stayed put received on average a 9% raise.
“Savvy CISOs can buck the trend of falling behind the market by utilizing third party data to educate HR teams on broader market comp,” Matt Comyns, co-founder and president at Artico Search, said in the blog post.
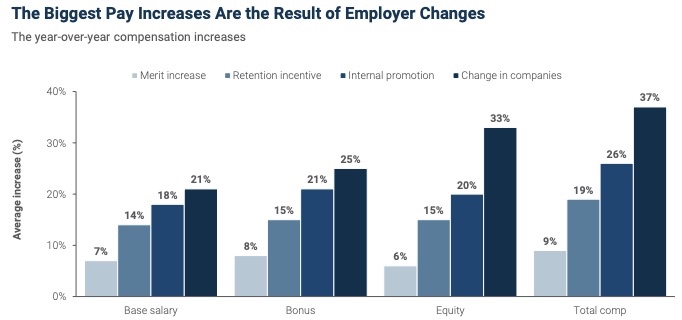
(Source: “2022 CISO Compensation Benchmark Report” from IANS Research and Artico Search, October 2022)
您如果想要了解更多信息,
- “Executive Recruiters Scrambling to Find Cybersecurity Leaders” (Hunt Scanlon Media)
- “64% of CISOs hired from outside, highlighting retention issues” (Venturebeat)
- “How To Handle Today’s High CISO Turnover” (Chief Executive)
- “7 CISO succession planning best practices” (TechTarget)
- “Why You Need A Cloud-Savvy CISO — And How To Find One” (Forbes)
2 – Cybersecurity pros’ wallets also benefit from talent crunch
And it’s not just CISOs who are reaping the benefits of the cybersecurity talent shortage. Cybersecurity pros in general are being showered with salary raises, professional development opportunities and other perks, such as remote work and flexible schedules.
According to a Robert Half survey of more than 230 technology hiring managers in the U.S., almost a third said finding cybersecurity pros is their biggest challenge, and 33% are willing to offer higher salaries as a way to compete for cybersecurity candidates.
Five IT security-related jobs that are in high demand right now are systems security administrator; network security engineer; systems security manager; data security analyst; and IT auditor, according to the human resources consulting firm.
And here are the average starting salaries for some of those “hot” cybersecurity roles in the U.S., according to Robert Half’s “2023 Salary Guide.”

(Source: Robert Half’s “2023 Salary Guide,” October 2022.)
In fact, the role of data security analyst ranked among the 12 hottest jobs in the overall U.S. employment market, a list that also included lawyer, cloud engineer, UX designer, controller and staff accountant.
How can hiring managers improve their recruitment of cybersecurity pros? Here’s a tip from Robert Half: Don’t stuff your job postings with a long list of required skills and credentials, as that’ll deter potentially good candidates from applying. People can be trained on the job, as long as they possess soft skills such as a willingness to learn, good time management, drive and determination.
您如果想要了解更多信息,
- “Hiring and retention challenges in cyber security persist” (ComputerWeekly)
- “Securing your organization by recruiting, hiring, and retaining cybersecurity talent” (McKinsey)
- “4 strategy game-changers for finding cybersecurity talent” (CSO Online)
- “90% of Security Leaders Warn of Skills Shortage” (Infosecurity Magazine)
- “Government CISOs making gains, but talent gap persists, survey finds” (StateScoop)
3 – CISA bangs on the next-gen MFA drum
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) this week urged all organizations to adopt multi-factor authentication (MFA) that’s “phishing-resistant,” as hackers keep getting better at bypassing traditional methods of MFA protection.
CISA recommends adopting the FIDO/WebAuthn authentication, a web-based API which is the result of a collaboration between the FIDO Alliance and the World Wide Web Consortium (W3C).
It’s the most widely adopted “phishing resistant” MFA method, with broad support in major browsers, operating systems and smartphones, CISA said in a new fact sheet, where it also details a public key infrastructure (PKI) method that isn’t as widely available.
The agency also released a companion fact sheet that focuses on ways to make more secure the traditional MFA method based on pushing notifications to a mobile device.
For more information read:
- “What is Phishing Resistant MFA?” (SANS Institute)
- “Next Level MFA: FIDO Authentication” (CISA)
- “What is phishing-resistant multifactor authentication? It’s complicated.” (Cybersecurity Dive)
- “CISA Publishes MFA Guidelines to Tackle Phishing” (Infosecurity Magazine)
You can also watch this CISA video:
4 – White House hosts global anti-ransomware summit
Highlighting the danger ransomware poses worldwide, the White House this week held its second international summit aimed at boosting global defenses against this destructive cyberthreat.
The Second International Counter Ransomware Initiative (CRI) Summit was attended by representatives from 36 countries, who jointly agreed to take a number of steps in the coming year, including:
- Establish the International Counter Ransomware Task Force (ICRTF), which will be led by Australia and focus on defusing unlawful finance activities of ransomware groups.
- Create a “fusion cell” at the Regional Cyber Defense Centre (RCDC), led by Lithuania and tasked with publishing reports on ransomware trends and mitigation measures.
- Deliver an “investigator’s toolkit,” with strategies to respond to incidents and disrupt ransomware activities, and with details on the playbooks of key ransomware actors.
- Actively and consistently engage with the private sector by sharing information and coordinating actions.
- Outline tactics, techniques and procedures for major ransomware players with “warning and mitigation measures.”
For more information, you can read the participants’ joint statement and the closing remarks by U.S. National Security Advisor Jake Sullivan, and watch this video from the two-day summit.
5 – U.K.’s cybersecurity agency IDs top threats
Meanwhile over in the U.K., the National Cyber Security Centre (NCSC) highlighted ransomware, supply chain security, unsophisticated cyber attacks and nation-state threats in its annual report.
Amidst multiple cyber threats, the biggest change in the country’s cybersecurity landscape came from Russia’s invasion of Ukraine, which prompted the NCSC to engage in a “huge effort” to boost the U.K.’s “whole of society” cyber resilience, according to agency CEO Lindy Cameron.
Here’s a closer look at the challenges highlighted by the NCSC in the report, which covers the 12-month period ending Aug. 31, 2022:
- Ransomware, which Cameron called “the most acute threat” to U.K. businesses and organizations
- Low-sophistication, high-volume “commodity” cybercrime, such as phishing and other cyber scams
- Wider availability and easier access to high-end tools and capabilities for committing cybercrime
- Threats to the software supply chain, as attackers try to compromise legitimate software-release channels to stealthily deliver malicious code
- Cyber espionage, destructive cyberattacks, intellectual property theft and political intervention from state actors, including Russia, Iran, North Korea and China
And here are some highlights of what the NCSC did during this 12-month period to help address the main cyber threats impacting the U.K.

(Source: U.K. National Cyber Security Centre’s “2022 Annual Review,” October 2022)
For more information, you can read an executive summary or the full text of the report, and watch Cameron’s video about it.
6 – Santander zooms in on “push payment” fraud in the U.K.
Alarmed at a boom in so-called “authorized push payment” (APP) scams in the U.K., Banco Santander’s wholly-owned subsidiary in the country has published a detailed proposal for tackling the problem.

(Credit: Santander UK)
To tackle APP scams, in which customers are duped into approving payments, Santander U.K. recommendations include:
- Sharpening banks’ ability to pinpoint fraud signs by capturing additional data points about transactions via new data sharing standards
- Requiring all payment service providers to adhere to a standard set of fraud rules
- Subjecting transactions to different levels of scrutiny, depending on their magnitude
- Requiring companies that criminals use to contact victims – such as telecoms and social media companies – to improve oversight of their platforms and networks
For more information about APP fraud:
- “Authorized Push Payments Surge to 75% of Banking Fraud (Infosecurity Magazine)
- “APP Fraud Is Fastest Growing Scam for One Good Reason” (PYMNTS)
- “What are Authorised Push Payment scams?” (U.K. Payment Systems Regulator)
- “Congress Drills Bank Brass on Authorized Push Payments Fraud” (PYMNTS)
- “Banks must do more to protect customers from APP scams” (This Is Money)
相关文章
- Cybersecurity Snapshot
- Executive Management
- Federal
- Government
- Public Policy





