Cybersecurity Snapshot: 6 Things That Matter Right Now

Topics that are top of mind for the week ending Oct. 14 | DevOps team culture is key for supply chain security | SecOps gets more challenging as attack surface expands | Weak credentials hurt cloud security | Incident responders grapple with stress | Security spending grows | And much more!
1 – Google’s DevOps report zooms-in on supply chain defense
In a sign of the times, Google’s annual “Accelerate State of DevOps” report – now in its eighth year – delves deeply for the first time on software supply chain security.
Here are major findings from the report, whose security survey questions were based on the defensive measures of the Supply Chain Levels for Software Artifacts (SLSA) framework and of the National Institute of Standards and Technology’s Secure Software Development Framework (SSDF.)
- While there is broad adoption of supply-chain security practices, with a majority of respondents having at least partially adopted every SLSA and SSDF practice, plenty of room for growth remains.
- DevOps teams with a culture marked by high trust, low blame and cooperation, as well as by a focus on performance, are more likely to successfully adopt security practices. In short: team culture plays a larger role than even technology in securing the software development lifecycle (SDLC.)
- That’s not to say that technology is irrelevant. In fact, the report found that having a pipeline for continuous integration and delivery (CI/CD) of software releases is critical for the adoption and success of supply chain security practices.
- However, high on developers’ wish list is being able to run scans on their workstations before sending code to the CI/CD pipeline, so they can assess the security of their software components – especially open source ones – earlier.
- More than half (56%) of respondents said that security practices slow down their application development process, proof that many DevOps teams can go further in reducing friction between security and development processes.
- Benefits of adopting supply-chain security processes go beyond the obvious reduction in security risks, and include having DevOps staffers that suffer from less burnout and are more likely to rate their organization as a great place to work.
For more information:
- Read a report summary or the full report from Google’s DevOps Research and Assessment (DORA) team
- Listen to a podcast interview with two of the authors
- Read coverage and analysis from ZDnet, Dark Reading, Silicon Angle, Cybersecurity Dive, DevClass and ITPro Today.
2 – SecOps is getting harder
If it feels like security operations processes are becoming thornier, it’s because they are – at least according to a recent survey from Enterprise Strategy Group.
According to an article about the study that ESG analyst Jon Oltsik published in CSO Magazine, 52% of respondents rated SecOps “more difficult” today than two years ago.
Key reasons cited by respondents include:
- A dynamic threat landscape that makes it difficult for security pros to plan and act proactively.
- An ever-expanding attack surface – 69% of organizations surveyed suffered a “cyber incident” stemming from an unknown or unmanaged internet-facing asset.
- An increase in the number and complexity of security alerts.
- Growth in public cloud usage.
- Difficulty dealing with security tool sprawl – 54% of respondents use 26 or more different security tools.
For more information about SecOps challenges and best practices:
- “What Is a Security Operations Center?” (CompTIA)
- “8 challenges every security operations center faces” (TechTarget)
- “Building a Security Operations Centre” (National Cyber Security Centre)
- “11 Strategies of a World-Class Cybersecurity Operations Center” (MITRE)
- “Best Practices for Setting Up a Cybersecurity Operations Center” (ISACA)
3 – Retail and hospitality sector hounded by credential harvesting
The theft of their staffers’ login information ranked as the top cyber threat currently affecting retailers and hospitality businesses.
That’s according to a new report from the Retail & Hospitality Information Sharing and Analysis Center (RH-ISAC), where cybersecurity pros in this sector gather to share information.
Here’s a graph from the “Retail & Hospitality ISAC Intelligence Trends Summary” report, showing the top reported threats by group members between May and August 2022.
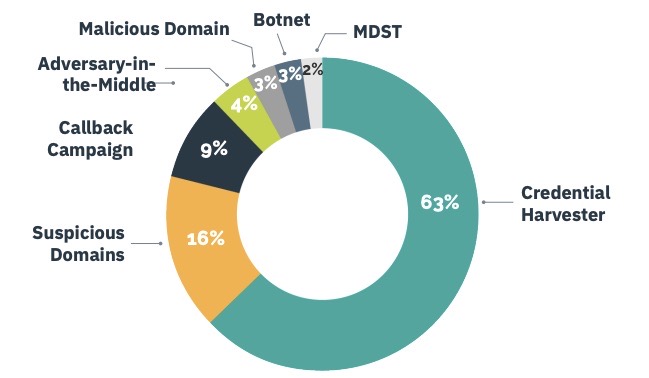
(Source: RH-ISAC’s “Retail & Hospitality ISAC Intelligence Trends Summary: May - August 2022” report)
In terms of malware threats, Emotet ranked first, with 33% of members reporting it, followed by Qakbot (13%) and Agent Tesla (11%.)
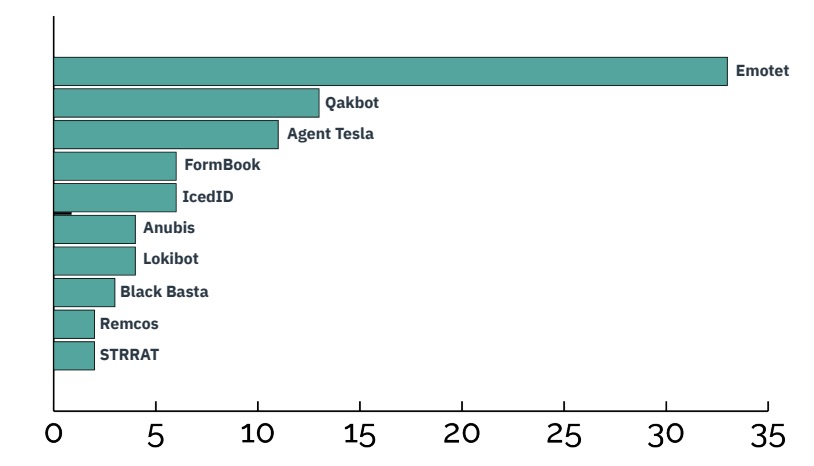
(Source: RH-ISAC’s “Retail & Hospitality ISAC Intelligence Trends Summary: May - August 2022” report)
The report also sheds light on the topics members are most interested in learning about, based on requests for information (RFIs) submitted to the group. Ranking first with 40% of the RFIs was security architecture, followed by risk management (27%), special interest and resilience (22%), security operations (9%) and threat intelligence (3%.)
Here’s more information about credential harvesting and how to prevent it:
- “Using Rigorous Credential Control to Mitigate Trusted Network Exploitation” (U.S. Cybersecurity & Infrastructure Security Agency - CISA)
- “MS-ISAC Security Primer – Securing Login Credentials” (Center for Internet Security)
- “Authentication Cheat Sheet” (Open Web Application Security Project - OWASP)
- “Why Are Authentication and Authorization So Difficult?” (Center for Internet Security)
- “Credential Stuffing Prevention Cheat Sheet” (OWASP)
- “Hacker Lexicon: What Is Credential Stuffing?” (Wired)
- “Identity-based cyberattacks are the leading cause of security breaches. Here’s how to stop them.” (Protocol)
4 – Top factor in cloud compromises? Hint: Re-read previous item.
Staying on topic, the “September 2022 Threat Horizons Report” from Google’s Cybersecurity Action Team is out with tons of insights, but this one in particular jumped out at us: The main factor in cloud compromises is – by a country mile – “weak or no credentials.”
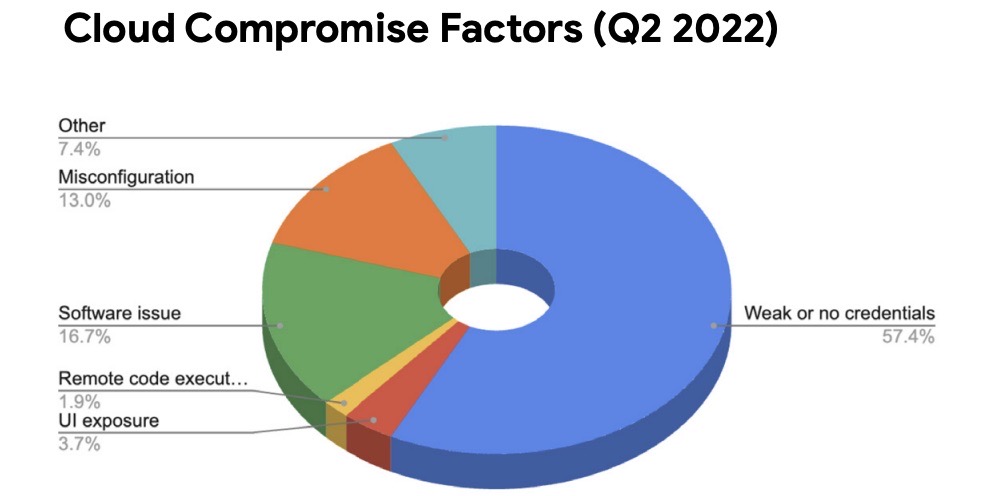
(Source: “September 2022 Threat Horizons Report” from Google’s Cybersecurity Action Team, Sept. 2022)
For more information, you can check out the full report, as well as commentary from Google Senior Security Advisor Anton Chuvakin
5 – Cyber incident responders: highly committed but very stressed out
A strong sense of duty and the opportunity to learn and solve problems drive cybersecurity incident responders. However, their stress levels are worsening due the weight of their responsibilities, stakeholder expectations and the increasing number and complexity of attacks.
Those findings come from the IBM Security Incident Responder Study which was conducted by Morning Consult and surveyed 1,107 cybersecurity incident responders in the U.S., U.K., Germany, Canada, Australia, France, Spain, Brazil, Japan and India.
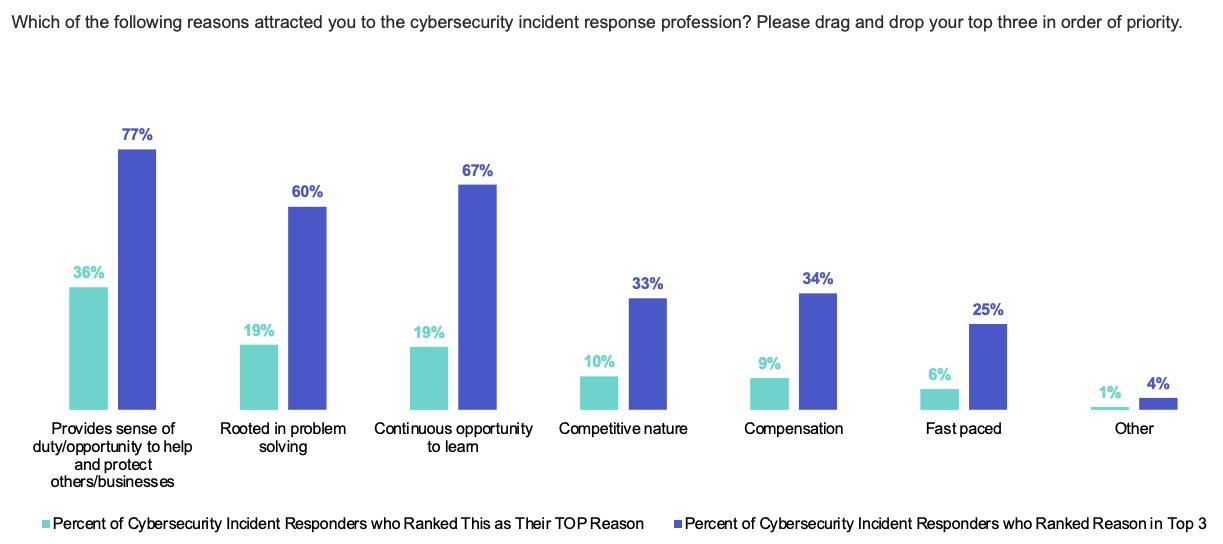
(Source: “IBM Security Incident Responder Study,” Oct. 2022)
Other findings from the report include:
- Most incident engagements last between two and four weeks on average, although the most stressful period is the first three days, when 12-hour days are common.
- Ransomware in particular was cited by 81% of respondents as a factor that has exacerbated their stress and anxiety.
- Almost 65% of respondents said they’ve sought mental health services as a result of their work, almost the same percentage who said their job causes them daily stress.
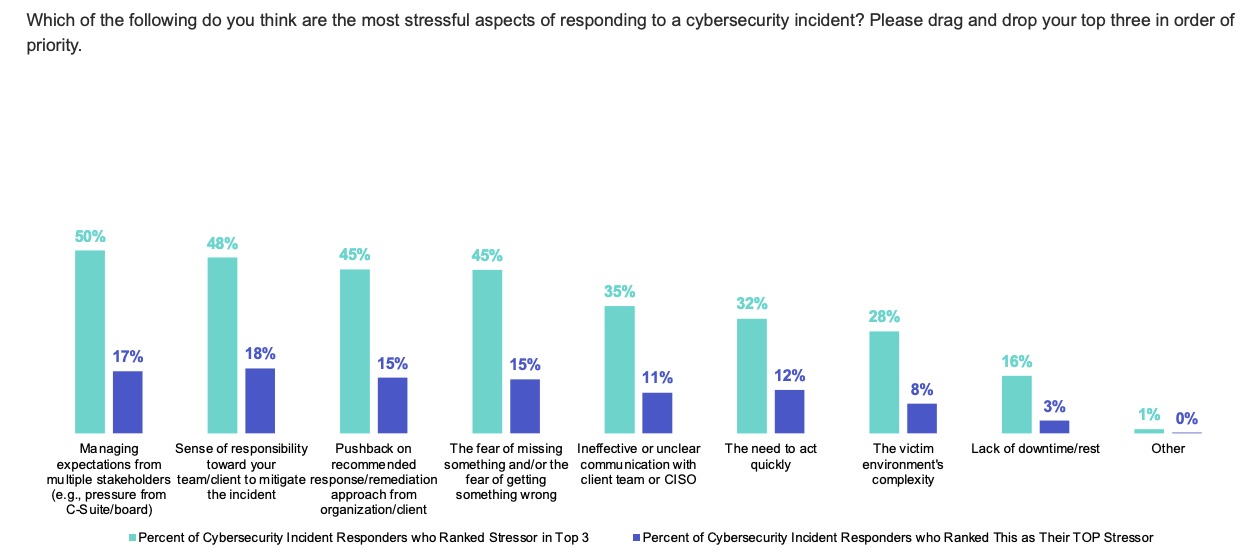
(Source: “IBM Security Incident Responder Study,” Oct. 2022)
Although the nature of the job is inherently stressful, organizations can take steps to lessen the burden on incident response teams. Here are two suggestions from the report.
- Develop detailed incident response plans and playbooks tailored to the organization, so that the required resources to properly respond to an incident are available.
- Simulate incident responses under pressure to not only rehearse but also identify steps and actions that can be improved.
For more information about the survey, read this IBM Community post and IBM blog, and check out coverage from Dark Reading, Cybersecurity Dive, Help Net Security, and MSSP Alert.
6 – Security to take top spot in 2023 software spending
IT departments plan to allocate the biggest slice of their 2023 software budgets to security products and services, narrowly edging out productivity applications, which traditionally have ranked number one.
That’s according to the “2023 State of IT” report from Spiceworks Ziff Davis (SWZD), which provides a comprehensive overview of IT budget plans and technology trends, based on a survey of 968 IT buyers from North America and Europe.
Increased concern about security is one of four key factors influencing IT budget growth in 2023, with significant boosts in spending in these security areas:
- Hardware-based authentication
- Protection of cloud workloads
- Operational technology (OT) security
- AI and machine learning security
- IoT security
“Organizations are increasingly seeing cybersecurity-related and information security risks for what they really are – a business issue, not a strictly technical issue,” Derek E. Brink, VP and Research Fellow at SWZD’s Aberdeen Strategy & Research division, said in the report.
Which of the following emerging security solutions are implemented at your organization, and which is it planning to implement?
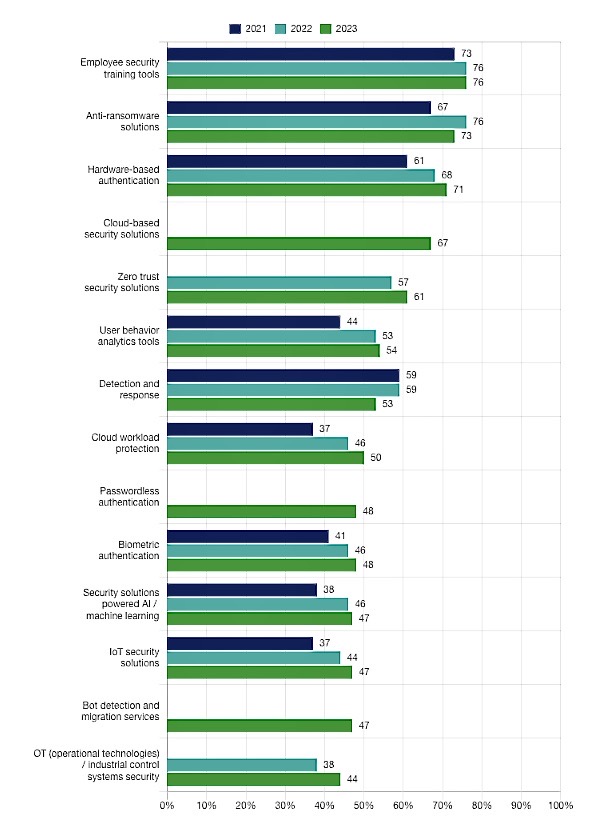
(Source: "“2023 State of IT” report from Spiceworks Ziff Davis, Sept. 2022)
For more information about the study, you can read a SWZD summary and blog, an Aberdeen blog, and coverage from TechRadar, PCMag and CIO Dive.
Related Articles
- Cloud
- Cybersecurity Snapshot
- DevOps
- Incident Response
- Security Frameworks
- Security Policy
- Vulnerability Management





