CVE-2021-26084: Atlassian Confluence OGNL Injection Vulnerability Exploited in the Wild

Recently disclosed critical flaw in Atlassian Confluence Server is being exploited in the wild by attackers. Organizations should apply patches immediately.
Background
On August 25, Atlassian published a security advisory for a critical vulnerability in its Confluence Server and Data Center software.
| CVE | Description | CVSSv3 | VPR* |
|---|---|---|---|
| CVE-2021-26084 | Confluence Server Webwork OGNL Injection | 9.8 | 9.7 |
* Please note: Tenable’s Vulnerability Priority Rating (VPR) scores are calculated nightly. This blog post was published on September 7 and reflects VPR at that time.
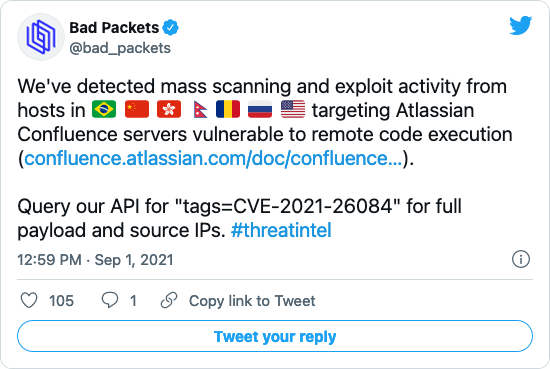
On September 1, one week after the advisory was published, Troy Mursch of Bad Packets detected attackers scanning for and attempting to exploit vulnerable servers.
Analysis
CVE-2021-26084 is an Object-Graph Navigation Language (OGNL) injection vulnerability in the Atlassian Confluence Webwork implementation. An unauthenticated, remote attacker could exploit this flaw by sending a specially crafted request to vulnerable endpoints on the Confluence Server or Data Center instance. Successful exploitation would allow an attacker to execute arbitrary code.
Initial confusion surrounding authentication requirement
When the vulnerability was first disclosed on August 25, the advisory stated that an authenticated attacker or “in some instances” an unauthenticated attacker — depending on the configuration — could exploit the flaw. However, in a subsequent update on September 4, Atlassian revised its advisory clarifying that authentication is not required to exploit the vulnerability and that in-the-wild exploitation had been observed.
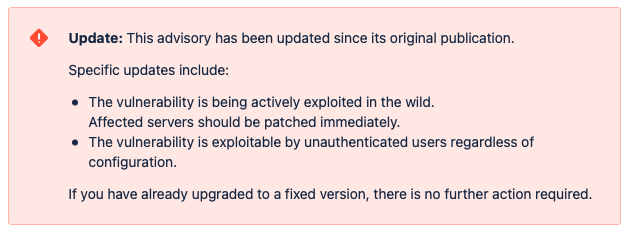
Image Source: Atlassian Confluence Advisory
Thousands of Confluence Servers are vulnerable to CVE-2021-26084
On September 2, Censys, a search engine for discovering internet devices, published a blog post analyzing the number of hosts vulnerable to CVE-2021-26084.
#CVE-2021-26084 is a critical severity remote code execution vulnerability affecting Atlassian Confluence. Censys analyzed the issue for global impact as part of our Rapid Response program.
— Censys (@censysio) September 2, 2021
We urge practitioners to patch as soon as possiblehttps://t.co/zGkVpRU1Tm
Initially, Censys found that over 12,000 servers were publicly accessible and vulnerable to this flaw on September 1. However, they’ve since observed a marked decrease in the number of vulnerable servers, down to 8,597 as of September 5.
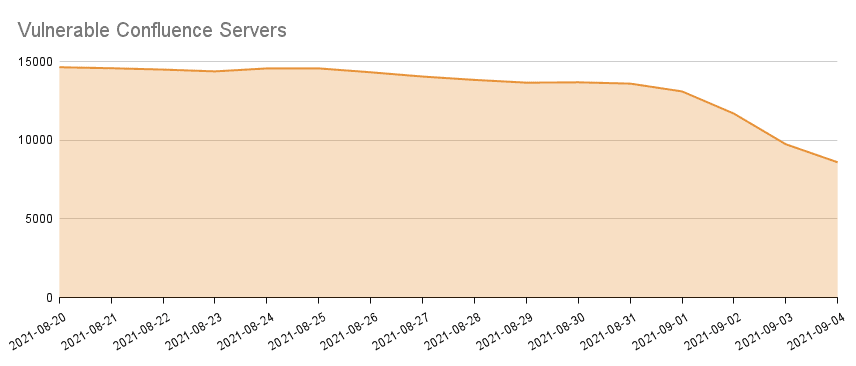
Image Source: Censys Blog
Attackers installing cryptocurrency miners on vulnerable Confluence servers
According to both Mursch and researcher Kevin Beaumont, attackers that have scanned for and exploited CVE-2021-26084 have been installing the XMRig cryptocurrency miner on vulnerable Confluence servers on both Windows and Linux. BleepingComputer reports they’ve reviewed a separate active exploit that attempts to install the Kinsing malware, which Trend Micro analyzed in November 2020.
Unpatched vulnerabilities remain valuable for cybercriminals months to years later
As active exploitation has begun, we know that historically attackers have found success in targeting flaws in Atlassian products like Confluence. For instance, CVE-2019-3396, a vulnerability in the Confluence Widget Connector that was patched in March 2019, was exploited in the wild in April 2019 by the GandCrab ransomware group and the AESDDoS botnet. Despite patches being available over two years ago, CVE-2019-3396 is listed as one of the Top Routinely Exploited Vulnerabilities according to a joint government advisory published in July.
Even with the observed decrease in the number of vulnerable Confluence servers, we expect to see continued exploitation attempts for CVE-2021-26084 in the coming weeks to months as other threat actors incorporate public exploits into their toolkits.
Proof of concept
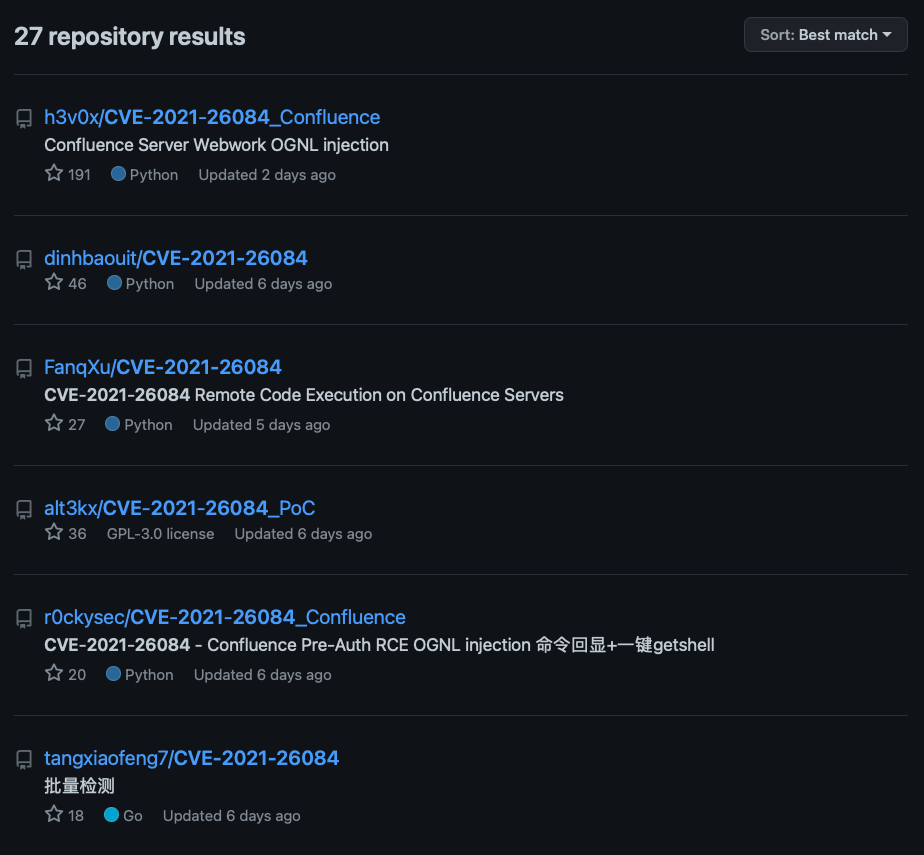
At the time this blog post was published, there were at least 27 repositories on GitHub containing proof-of-concept code to detect and/or exploit CVE-2021-26084 as well as write-ups about the flaw.
Solution
Atlassian has released patches for CVE-2021-26084. In its advisory, Atlassian confirms that this flaw affects a number of branches of Confluence and Data Center server instances:
| Affected Branch/Versions | Fixed Branch/Version |
|---|---|
| 4.x.x | Upgrade to a fixed version below |
| 5.x.x | Upgrade to a fixed version below |
| 6.0.x, 6.1.x, 6.2.x, 6.3.x, 6.4.x, 6.5.x, 6.6.x, 6.7.x, 6.8.x, 6.9.x, 6.10.x, 6.11.x, 6.12.x, 6.14.x, 6.15.x | Upgrade to a fixed version below |
| 7.0.x, 7.1.x, 7.2.x, 7.3.x, 7.5.x, 7.6.x, 7.8.x, 7.9.x, 7.10.x | Upgrade to a fixed version below |
| 6.13.22 and lower | 6.13.23 |
| 7.4.10 and lower | 7.4.11 |
| 7.11.5 and lower | 7.11.6 |
| 7.12.4 and lower | 7.12.5 |
Please note that Atlassian Confluence Cloud is not affected by this vulnerability.
Atlassian advises customers to upgrade to the newest Long Term Support (LTS) release available, which is Confluence 7.13. If upgrading to a LTS release is not currently feasible, Atlassian has provided point releases for 6.13.x, 7.4.x, 7.11.x and 7.12.x.
Temporary workaround available
If applying the available patches is not possible at this time, Atlassian has provided update scripts along with instructions for both Windows and Linux Confluence customers in order to mitigate the flaw on their servers. Please note that these scripts should only be used as a temporary workaround until patches can be applied.
Identifying affected systems
A list of Tenable plugins to identify this vulnerability can be found here.
Get more information
- Atlassian Advisory for CVE-2021-26084 in Confluence Server and Data Center
- Censys Blog Post on CVE-2021-26084
- GitHub Repositories for CVE-2021-26084
- Joint Advisory from CISA, FBI, ACSC and NCSC on Routinely Exploited Vulnerabilities
- Tenable Blog Post on CVE-2019-33396 in Confluence Server and Data Center Widget Connector
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
Related Articles
- Vulnerability Management





