CVE-2020-0796: "Wormable" Remote Code Execution Vulnerability in Microsoft Server Message Block SMBv3 (ADV200005)
Critical unpatched “wormable” remote code execution (RCE) vulnerability in Microsoft Server Message Block 3.1.1 (SMBv3), dubbed EternalDarkness, disclosed by Microsoft.
Update 03/13/2020: The Proof-of-concept section has been updated to reflect the public availability of an exploit script that can trigger a crash on a vulnerable system.
Update 03/12/2020: The Analysis, Proof-of-concept, Solution and Identifying affected systems sections have been updated. Microsoft released an official advisory for CVE-2020-0796 including a security patch that addresses the flaw.
背景
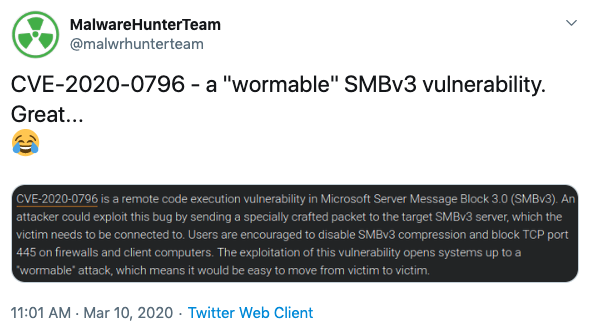
On March 10, Microsoft published ADV200005, an advisory for a critical RCE vulnerability in Microsoft Server Message Block 3.1.1 (SMBv3). Details about this vulnerability were originally disclosed accidentally in another security vendor’s blog for March’s Microsoft Patch Tuesday. Soon after their blog post was published, the vendor removed reference to the vulnerability, but security researchers already seized on its accidental disclosure.
Microsoft eventually acknowledged the vulnerability publicly and published its advisory for it.
Microsoft is aware of a RCE vulnerability in the way that the SMBv3 protocol handles certain requests. If you wish to be notified when updates for this vulnerability are available, please follow the guidance in the advisory linked here: https://t.co/x5Z658xQ6t
— Security Response (@msftsecresponse) March 10, 2020
分析
Microsoft did not assign a CVE identifier for this vulnerability in ADV200005. However, the accidental disclosure of the vulnerability identified it as CVE-2020-0796, which was later confirmed on March 12 when Microsoft published an out-of-band update.
According to Microsoft, the vulnerability exists in the way the SMBv3 handles certain requests. For SMBv3 Server, an unauthenticated attacker could exploit this vulnerability by sending a specially crafted packet to a vulnerable SMBv3 Server. For SMBv3 Client, an attacker would need to convince a user to connect to a malicious SMBv3 Server they’ve configured.
Successful exploitation of the vulnerability would grant the attacker arbitrary code execution in both SMB Server and SMB Client.
Based on an intrusion prevention system (IPS) rule released by FortiGuard Labs, the flaw appears to stem from a buffer overflow vulnerability, which occurs due to an error in the handling of compressed data packets.
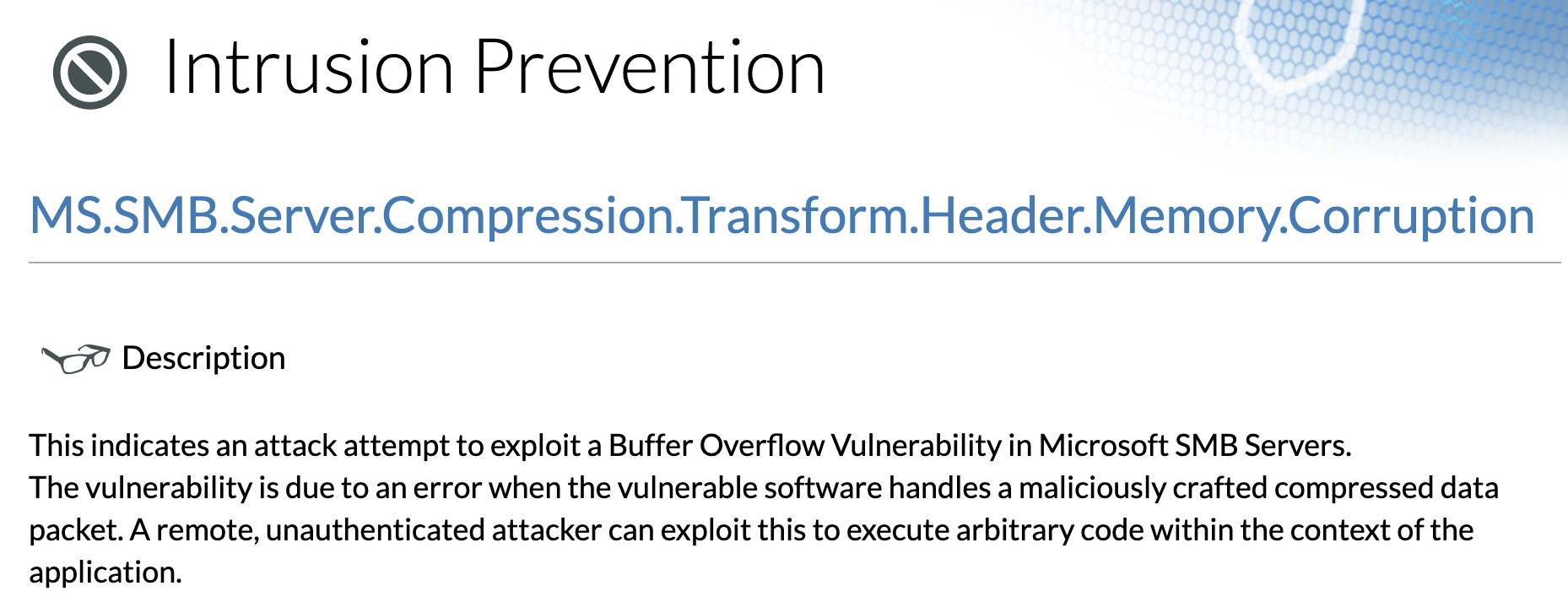
Image source: Fortiguard Labs Threat Encyclopedia
This latest vulnerability evokes memories of EternalBlue, most notably CVE-2017-0144, an RCE vulnerability in Microsoft SMBv1 that was used as part of the WannaCry ransomware attacks. It’s certainly an apt comparison, so much so that researchers are referring to it as EternalDarkness. However, there is currently little information available about this new flaw, and the time and effort needed to produce a workable exploit is unknown.
it's okay the official Gossi name is EternalDarkness which doesn't sound super weird at all
— Kevin Beaumont (@GossiTheDog) March 10, 2020
概念验证
At the time this blog post was published, there was no proof-of-concept (PoC) publicly available. However, several researchers have since published PoC demos using CVE-2020-0796 to create a denial of service condition and local privilege escalation.
Marcus Hutchins, researcher for Kryptos Logic, known for his efforts to thwart the spread of the Wannacry ransomware, created a proof-of-concept demonstrating a denial of service utilizing CVE-2020-0796 to cause a blue screen of death.
Our Telltale research team will be sharing new insights into CVE-2020-0796 soon. Until then, here is a quick DoS PoC our researcher @MalwareTechBlog created. The #SMB bug appears trivial to identify, even without the presence of a patch to analyze. https://t.co/7opHftyDh0 @2sec4u pic.twitter.com/0H7FYIxvne
— Kryptos Logic (@kryptoslogic) March 12, 2020
Researchers at SophosLabs have also created a proof-of-concept using CVE-2020-0796 to elevate privileges on a compromised system.
As a MAPP member we were restricted from sharing what we knew about the bug until Microsoft released its update this morning for CVE-2020-0796. Our Offensive Research team did manage to develop a proof-of-concept exploit for one way to exploit the bughttps://t.co/Yb6O7jhAHi
— SophosLabs (@SophosLabs) March 12, 2020
On March 13, a PoC exploit script was published to GitHub that can trigger a BSoD on a vulnerable system. The README file in the repository notes that with “further work, this could be developed into a RCE exploit.”
解决方案
The following versions of Microsoft Windows and Windows Server are affected.
| 产品 | Version |
|---|---|
| Windows Server | Version 1903 (Server Core Installation) |
| Windows Server | Version 1909 (Server Core Installation) |
| Windows 10 | Version 1903 for 32-bit Systems |
| Windows 10 | Version 1903 for ARM64-based Systems |
| Windows 10 | Version 1903 for x64-based Systems |
| Windows 10 | Version 1909 for 32-bit Systems |
| Windows 10 | Version 1909 for ARM64-based Systems |
| Windows 10 | Version 1909 for x64-based Systems |
On March 12, Microsoft released a patch to address this vulnerability. We strongly encourage organizations and users to apply these patches as soon as possible.
Microsoft had originally provided workaround instructions as part of their initial advisory on March 11. These workaround instructions include a PowerShell command that disables compression for SMBv3 Server to prevent attackers from exploiting the vulnerability.
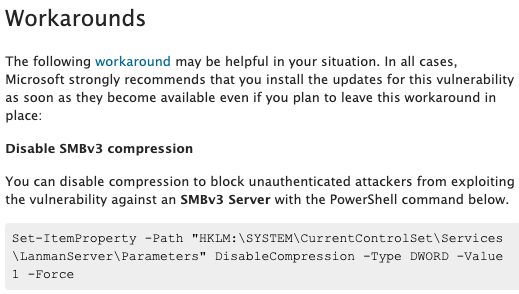
In addition to disabling compression, Microsoft advises blocking inbound and outbound traffic on TCP port 445 on the perimeter firewall. The Computer Emergency Response Team Coordination Center (CERT/CC) also advises verifying that SMB connections from the internet “are not allowed to connect inbound to an enterprise LAN.”
While these workarounds will prevent exploitation of SMBv3 Server, it is important to note that SMBv3 Client will remain vulnerable until patches are applied.
识别受影响的系统
A list of Tenable plugins to identify this vulnerability will appear here as they’re released.
获取更多信息
- Microsoft Security Advisory for CVE-2020-0796
- ADV200005: Microsoft Security Advisory for SMBv3 Remote Code Execution Flaw
- CERT Coordination Center Vulnerability Note, VU#872016
- Microsoft KB Article KB4551762
加入 Tenable Community 中的 Tenable 安全响应团队
了解有关 Tenable 这款首创 Cyber Exposure 平台的更多信息,全面管理现代攻击面。
获取 30 天免费试用版 Tenable.io Vulnerability Management。
相关文章
- Vulnerability Management




