by Josef Weiss
January 19, 2022
Ransomware attacks leverage well-known and established software vulnerabilities and poor cyber hygiene. Successful ransomware attacks can cripple an organization with increased costs and lost revenue. There are many contributing factors to the upward trend of ransomware. The most important is the large number of software vulnerabilities and misconfigurations, along with Active Directory (AD) weaknesses that enable attackers to escalate privileges. Threat actors leverage poor cyber hygiene to their advantage to gain a foothold and propagate attacks. Ransomware has been very profitable for organized crime, which targets lucrative businesses that can afford large payouts. Many organizations purchase ransomware insurance to mitigate the cost of a breach, but insurers are starting to push back against large payouts if the organization is found to be negligent in following industry security guidance.
Ransomware is a symptom of poor cyber hygiene and security awareness, which can impact operational availability and lead to increased cost. Comprehensive and regularly tested Disaster Recovery and Data Recovery plans go a long way toward combating the effects of ransomware and other threats to the business. This dashboard highlights a path forward with an in-depth focus on cyber hygiene by enabling IT staff to focus on vulnerabilities that could have the most impact to the organization in the event of a ransomware attack. For more information, see the Tenable blog: Focus on the Fundamentals: 6 Steps to Defend Against Ransomware.
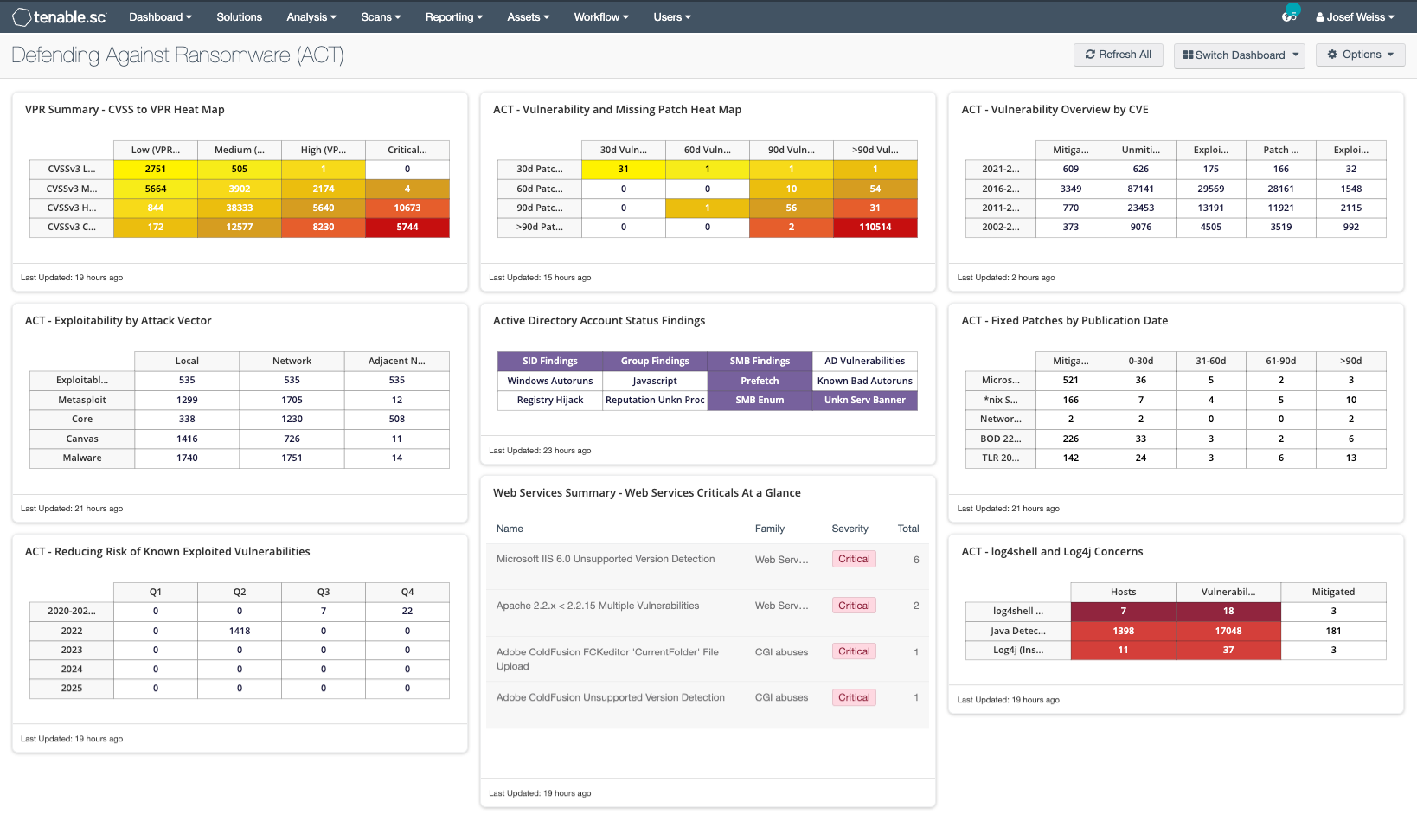
The first row of this dashboard indicates the most significant areas of concern. Displayed in the first column are vulnerabilities that have a published exploit. The middle column displays the current hygiene state. The vulnerability mitigation state is shown in the right column.
Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives. Tenable.sc discovers and analyzes assets continuously to provide an accurate and unified view of an organization’s security posture.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Threat Detection & Vulnerability Assessments.
The dashboard requirements are:
- Tenable.sc: 5.20.0
- Nessus: 10.0.2
This dashboard contains the following components:
- CVSS to VPR Heat Map - This widget provides a correlation between CVSSv3 scores and VPR scores for the vulnerabilities present in the organization.
- ACT - Exploitability by Attack Vector - This widget displays exploitable vulnerabilities by the CVSS Exploitability Metric Vectors: AV:N (Network), AV:A (Adjacent Network), and AV:L (Local).
- ACT - Reducing Risk of Known Exploitable Vulnerabilities - This matrix displays vulnerability totals for vulnerabilities past due in columns by quarter and in row by year for vulnerabilities.
- ACT - Vulnerability and Missing Patch Heat Map - This widget provides a correlation between Patch Published dates and Vulnerability Published dates for the vulnerabilities present in the organization.
- ACT - Active Directory Account Status Findings - This component provides easy access to several plugins used to collect information about user accounts and security identifiers (SID).
- Web Services Summary - Web Services Criticals at a Glance - This table component provides analysts with a listing of the critical vulnerabilities for web service platforms in the organization.
- ACT Vulnerability Overview by CVE - This matrix assists organizations with mapping mitigation progress and presents data to determine whether organizational SLAs are being met.
- ACT - Fixed Patches by Publication Date - This matrix assists organizations with mapping mitigation progress and presents data to determine whether organizational SLAs are being met
- ACT - log4shell and Log4j Concerns - The log4shell - Log4j Concerns indicator matrix alerts organizations to potential concerns regarding the Log4j vulnerability.