Reduce Cyber Risk To Cloud Infrastructure, Identities and Workloads
Close cloud exposure by connecting the dots between misconfigurations, vulnerabilities and excessive permissions with our Cloud-Native Application Protection Platform (CNAPP).
See How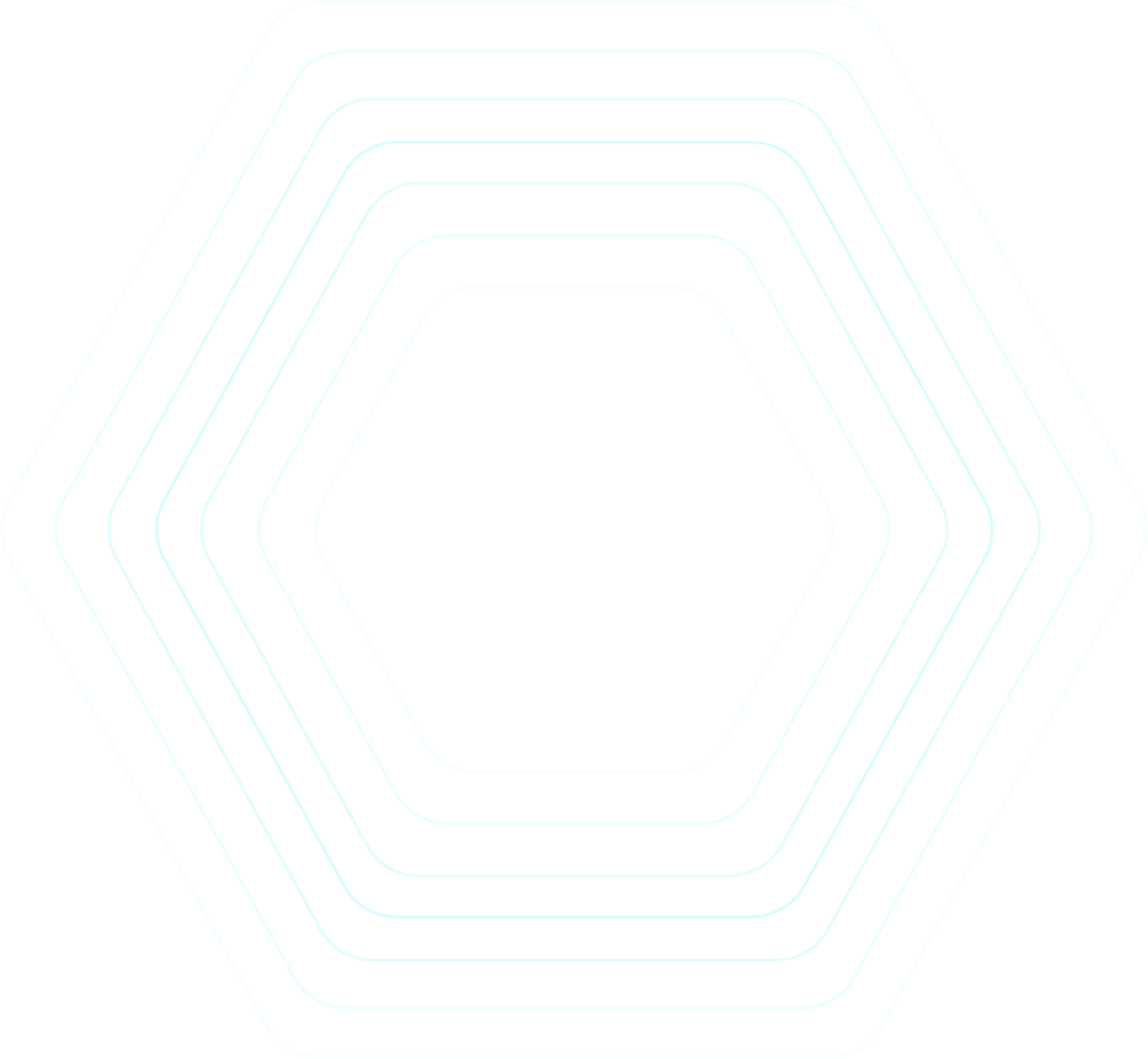
Consolidate and Simplify Your Cloud Security
Empower everyone
with relevant insights in a simplified, role-based, user interface.
Prioritize actions
based on full-stack exposure analysis.
Automate compliance
and audit reporting.
Makefixes faster
with automated remediation.
Unify Siloed Tools With Tenable Cloud Security
Securing multiple clouds running different types of workloads is complex enough without the stress of piecing together data from many point tools. Tenable Cloud Security offers market-leading CWP, CSPM, CIEM, CDR, KSPM, IaC, JIT and more in a unified CNAPP solution with a modern and simple user experience.
Agentless Workload Scanning (CWP)
Efficiently scan workloads including virtual machines (VMs), container images, runtime containers and serverless functions, with the market leader in vulnerability management. Detect exposed secrets, sensitive data, malware and misconfigurations.
了解详情
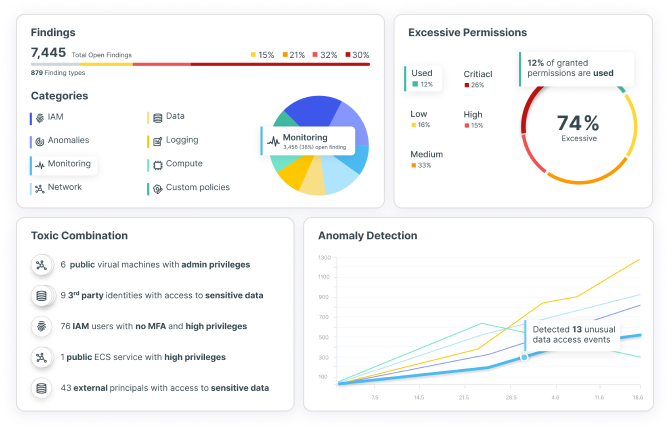
Compliance and Reporting (CSPM)
Continuously review cloud environment settings and configurations, maintaining regulatory compliance across multi-cloud environments. Report on CIS, HIPAA, NIST, PCI-DSS, GDPR and other frameworks, and custom checks.
了解详情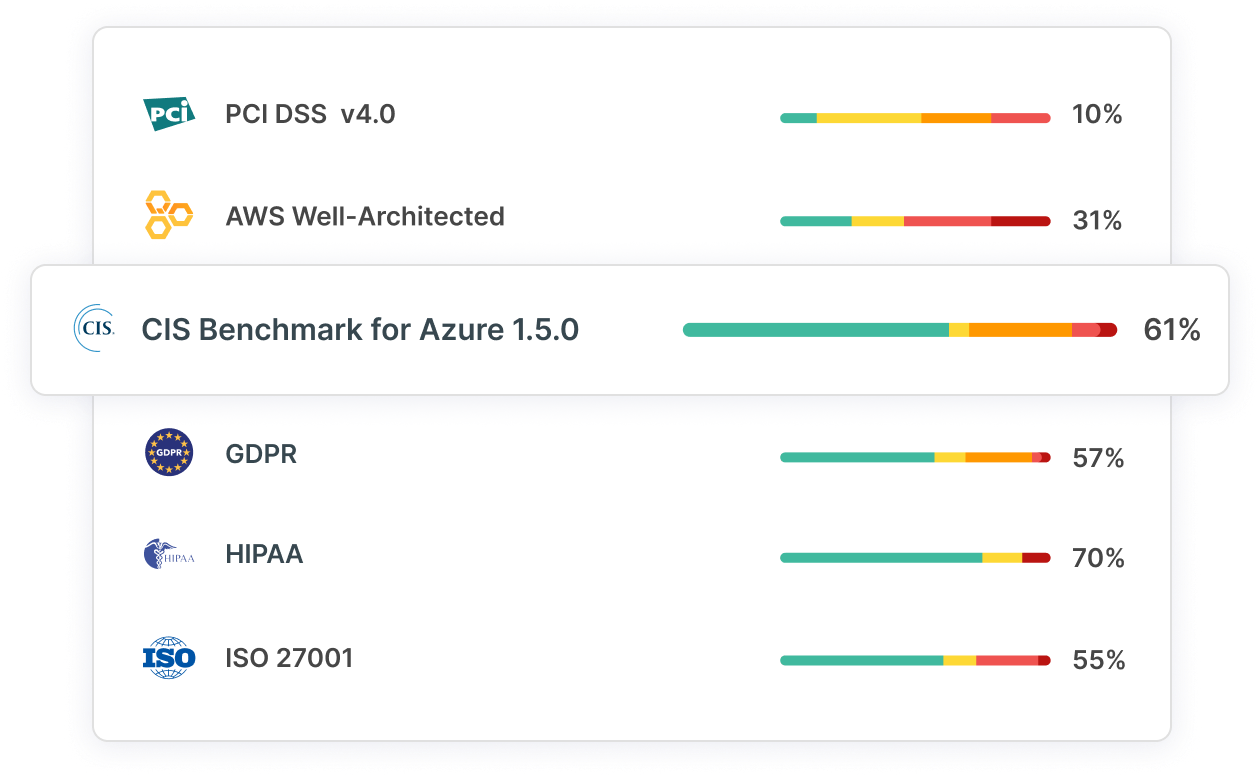
Cloud Infrastructure and Entitlements Management (CIEM) Security
Secure all identities (human and machine) and resources with best-of-breed entitlements management. Detect risky permissions and toxic mixes, and enforce least privilege including through Just-in-Time (JIT) access.
了解详情
Threat Detection and Response (CDR)
Automate threat detection with continuous behavioral analysis and anomaly detection based on built-in and custom policies. Investigate user activities using one of the best activity logs on the market, with intuitive query tools.
了解详情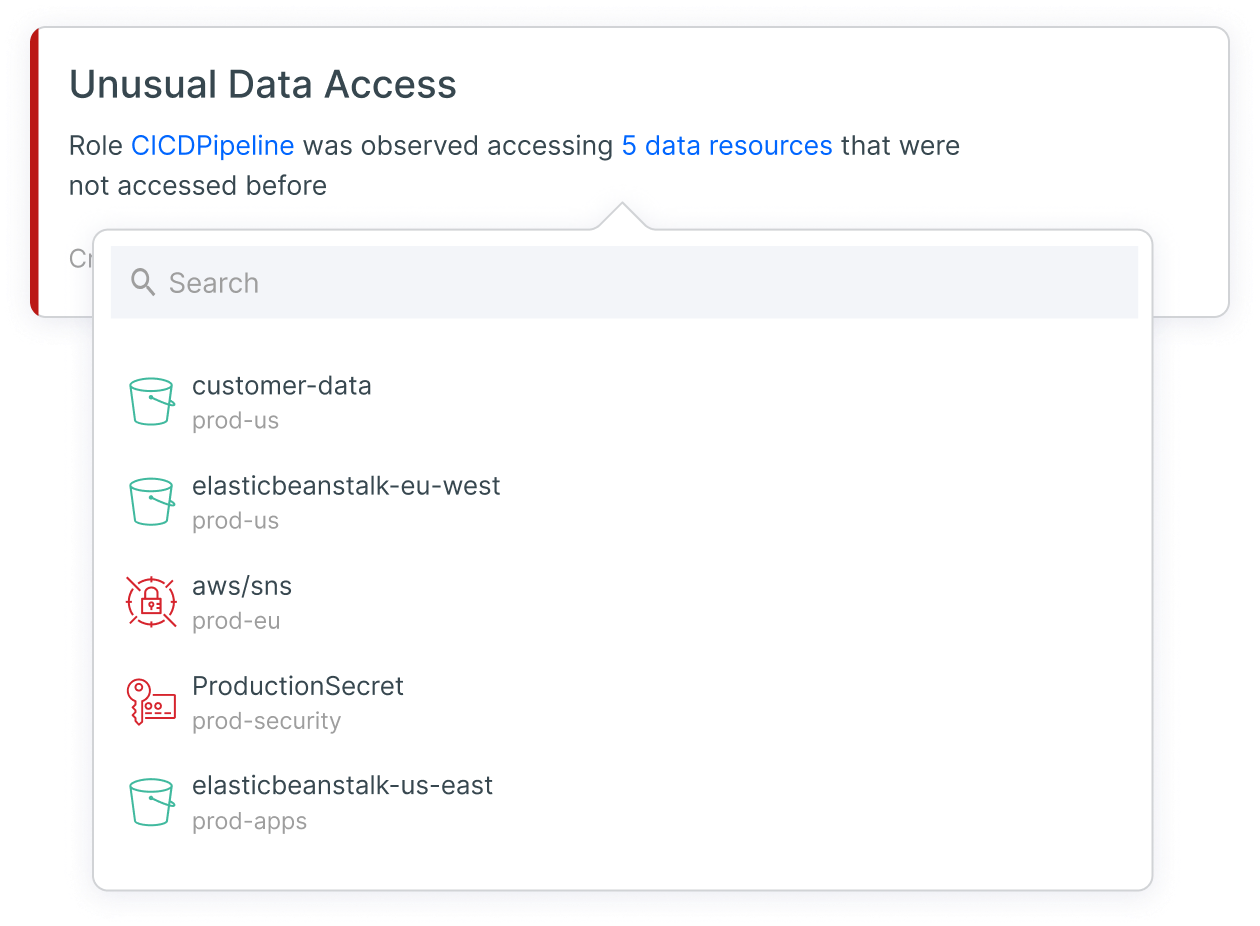
Kubernetes Security (KSPM)
Reveal, prioritize and remediate security gaps and automate compliance for Kubernetes clusters. Unify visibility into K8s container configurations and empower stakeholders with mitigation guidance.
了解详情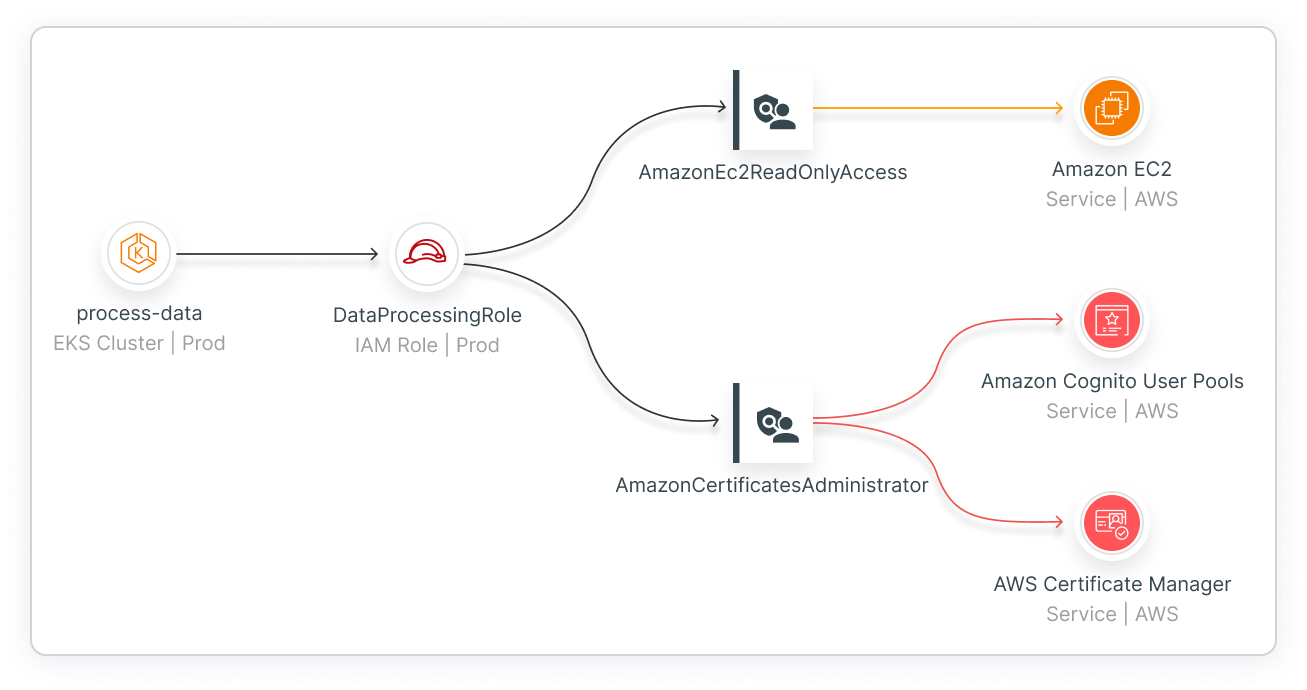
基础设施即代码安全 (IaC)
Implement shift-left security by scanning, detecting and fixing flaws in infrastructure as code. Reveal and remediate prioritized cloud risks in context and notify teams via integrations with ticketing and collaboration tools.
了解详情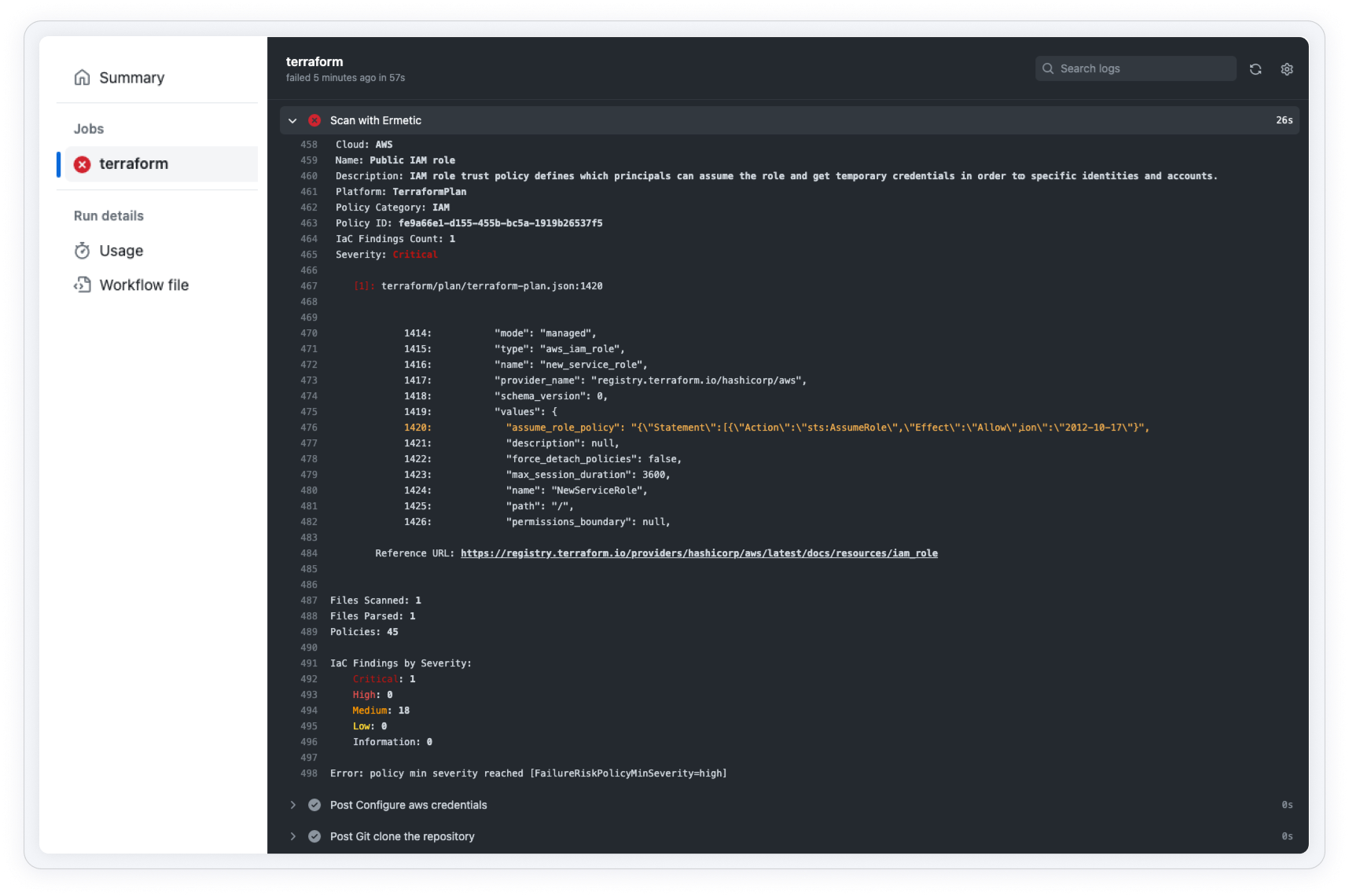
Real World Results
Customers across the globe use Tenable to reduce risks in minutes, empower teams with cloud security expertise and drive least privilege access at scale.

Aidoc gives its busy DevOps teams added IAM risk context, to better mitigate risks with minimal disruption.
Read the Story
Demyst met a key customer requirement for Just- in- Time (JIT) and improved access control in their complex environment.
Read the Story
Latch has automated periodic audits on all AWS IAM permissions, avoiding the expense of a third party Privileged Access Management platform.
Read the Story
Bilfinger automates GDPR compliance for Azure and AWS, providing actionable insights and ensuring least privilege access.
Read the Story
AppsFlyer hardened their cloud environment by integrating least privileged policies into the CI/CD pipeline.
Read the Story
Intelycare has eliminated exhaustive manual processes and reduced risks in minutes instead of two to three months.
Read the Story“Within an hour of starting our proof of concept we were able to confirm that the Tenable Cloud Security solution performed as promoted.”- DEMYST
Exposure Management That Extends Beyond the Cloud
Combine Tenable Cloud Security with the Tenable One Exposure Management Platform to continually manage exposure across the cloud, on-premise, and critical infrastructure – and the threats that lurk between them. Consolidate efforts to reduce cyber risk across your entire attack surface – without adding vendors or complexity.
了解详情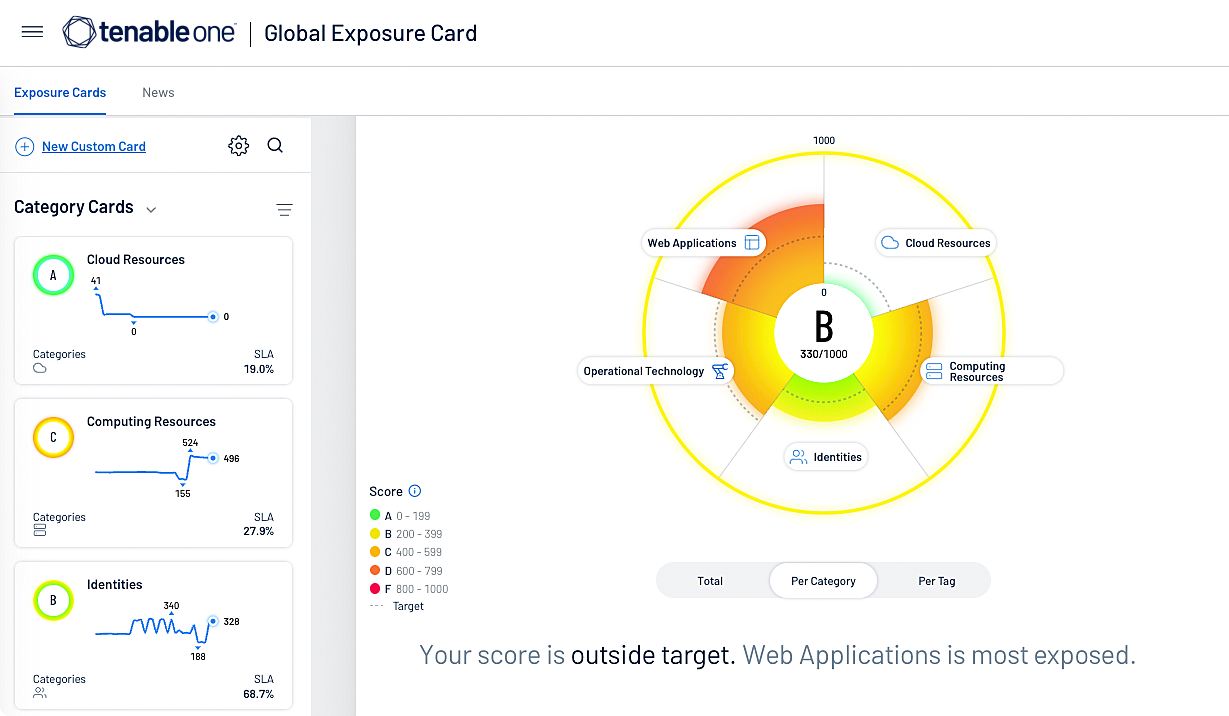
申请演示 Tenable Cloud Security
卓越的云安全随时听从您的调遣!
我们将向您展示 Tenable Cloud Security 如何帮助您提供多云资产发现、经过优先级分析的风险评估和自动化合规/审计报告。
- Tenable Cloud Security
 AWS
AWS Azure
Azure Google Cloud
Google Cloud

