Tenable 总结 Microsoft 2019 年 8 月星期二补丁包:DejaBlue

Microsoft’s August 2019 Security Updates, released on August 13, address over 90 vulnerabilities, 29 of which are critical.
Microsoft’s August 2019 Patch Tuesday release contains updates for 93 CVEs, 29 of which are rated Critical. This month brings patches for the usual suspects, namely the various flavors of Microsoft Windows, Office Products, Browsers IE and Edge, as well as Microsoft Dynamics, to name a few. As always, we recommend administrators take immediate action and ensure patches are applied across your organization. In cases where immediate patching is not an option, mitigation steps should be followed as per Microsoft’s recommendations. While none of the CVE’s this month appears to be exploited in the wild yet, several are likely to be exploited. Here, we break down and highlight a few of the most important CVEs from this month’s release.
CVE-2019-1181 & CVE-2019-1182 & CVE-2019-1222 & CVE-2019-1226 | Remote Desktop Services Remote Code Execution Vulnerability
Coming mere months after the May release of CVE-2019-0708 (BlueKeep), Microsoft released patches for four critical remote code execution vulnerabilities in Remote Desktop Services, dubbed DejaBlue by researcher Michael Norris. Exploitation requires little more than sending a specially crafted request to a targeted system’s Remote Desktop Service via RDP. The vulnerability can be exploited pre-authentication and requires no user interaction, making these bugs incredibly dangerous. Successful exploitation would allow an attacker to execute arbitrary code on a targeted host. CVE-2019-1181 and CVE-2019-1182 both offer mitigation options from Microsoft, similar to those offered around BlueKeep; Enabled Network Level Authentication (NLA) and Block TCP port 3389 at the perimeter firewall (Assuming the default port is in use on your hosts). While Microsoft notes these have not been exploited, it’s very likely that a Proof of Concept (PoC) will surface in the near future.
Additionally, three related CVEs were patched affecting Windows Remote Desktop Protocol. CVE-2019-1223 is a Denial of Service (DoS) vulnerability, while CVE-2019-1224 and CVE-2019-1225 are both information disclosure vulnerabilities. While Microsoft only rates these three vulnerabilities as important, it’s encouraging to see so much focus around RDP in the wake of BlueKeep and improving the security of a crucial component in Windows.
CVE-2019-0736 | Windows DHCP Client Remote Code Execution Vulnerability
A memory corruption vulnerability exists in the Windows DHCP client. A remote unauthenticated attacker could send a malicious DHCP response to a vulnerable machine, which the target then executes as code with SYSTEM permissions. DHCP also saw an update for CVE-2019-1213, a memory corruption vulnerability in Windows Server DHCP that could lead to remote code execution, along with two Denial of Service Vulnerabilities CVE-2019-1206 and CVE-2019-1212.
CVE-2019-1162 | Windows ALPC Elevation of Privilege Vulnerability
An elevation of privilege vulnerability exists in the Windows Operating System Advanced Local Procedure Call (ALPC). If an attacker has gained login access via some other means to a vulnerable host, that attacker could then execute malicious code that runs with SYSTEM permissions, rather than being restricted by the current user’s session permissions. CVE-2019-1162 is credited to Tavis Ormandy of Google Project Zero, who today published details of the work around finding the flaw. In addition to the research, Tavis also released a tool to ease in finding these flaws, and we expect to see more on this front in future months.
CVE-2019-1201 & CVE-2019-1205 | Microsoft Word Remote Code Execution Vulnerability
A remote code execution vulnerability exists in Microsoft Word. A specially crafted file could perform actions and run commands as the current user. Successful exploitation would require social engineering to get the target user to execute a malicious file, either through sending that file to the targeted user, or hosting the malicious file on a website with which the target user interacts. This vulnerability still requires the end user to open the malicious Word file to be executed. An interesting detail found in the advisories: Microsoft Outlook Preview Pane is an attack vector for these vulnerabilities. A related CVE, CVE-2019-1200 in Microsoft Outlook, could also lead to remote code execution by enticing a user to open a specially crafted file.
CVE-2019-0965 | Windows Hyper-V Remote Code Execution Vulnerability
A remote code execution vulnerability exists when Hyper-V on a host server fails to properly validate input from an authenticated user on a guest operating system. While exploitation does require the attacker to be able to execute a crafted application on a guest operating system, this highlights the dangers of insider threats. While exploitation is less likely in this scenario, Microsoft still rates the severity as Critical, since arbitrary code could be executed on the host operating system.
Tenable 解决方案
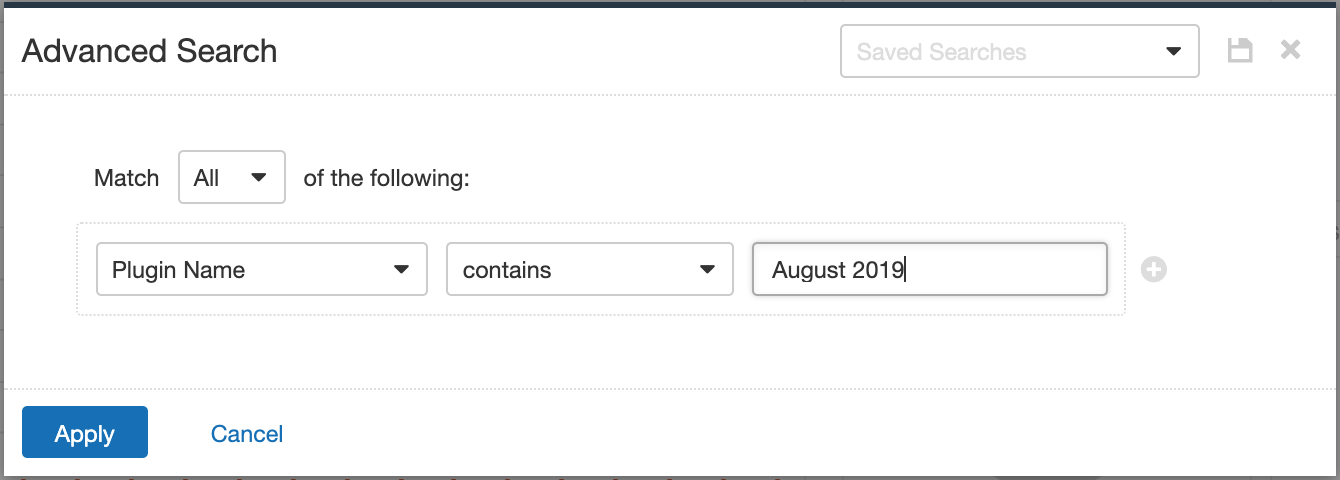
Users can create scans that focus specifically on our Patch Tuesday plugins. From a new advanced scan, in the plugins tab, set an advanced filter for Plugin Name Contains August 2019.
With that filter set, click on the plugin families to the left, and enable each plugin that appears on the right side. Note that if your families on the left say Enabled then that means all of the plugins in that family are set. Disable the whole family before selecting the individual plugins for this scan. Here’s an example from Tenable.io:
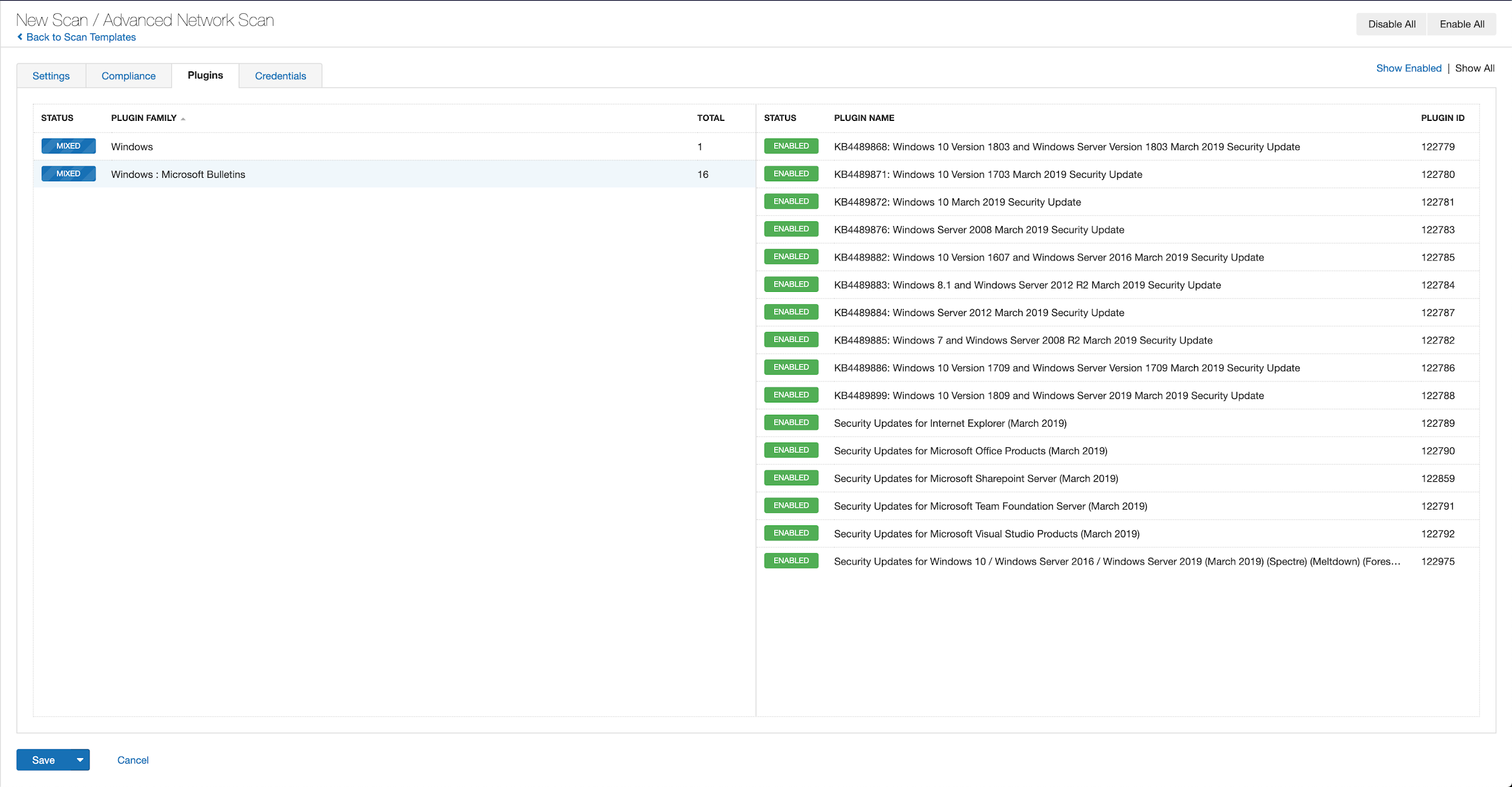
A list of all of the plugins released for Tenable’s August 2019 Patch Tuesday update can be found here.
了解详情:
相关文章
- Threat Intelligence
- Threat Management
- Vulnerability Management
- Vulnerability Scanning







