Microsoft’s August 2021 Patch Tuesday Addresses 44 CVEs (CVE-2021-26424, CVE-2021-36948)
Microsoft addresses 44 CVEs in its August Patch Tuesday release, including two vulnerabilities publicly disclosed, and one zero-day exploited in the wild.
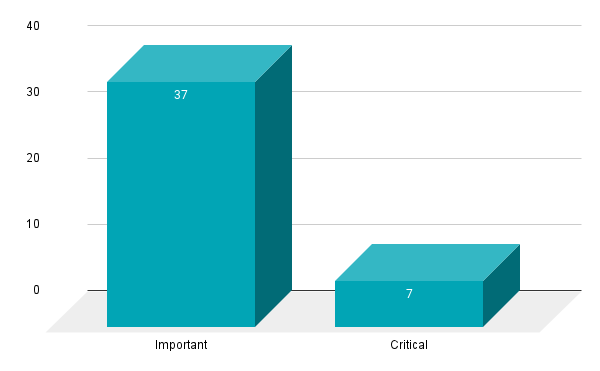
- 7Critical
- 37Important
- 0Moderate
- 0Low
Microsoft patched 44 CVEs in the August 2021 Patch Tuesday release, including seven CVEs rated as critical and 37 rated as important. This is the second time in 2021 that Microsoft has patched less than 50 vulnerabilities in a Patch Tuesday release.
This month’s update includes patches for:
- .NET Core & Visual Studio
- ASP .NET
- Azure
- Azure Sphere
- Microsoft Azure Active Directory Connect
- Microsoft Dynamics
- Microsoft Graphics Component
- Microsoft Office
- Microsoft Office SharePoint
- Microsoft Office Word
- Microsoft Scripting Engine
- Microsoft Windows Codecs Library
- Remote Desktop Client
- Windows Bluetooth Service
- Windows Cryptographic Services
- Windows Defender
- Windows Event Tracing
- Windows Media
- Windows MSHTML Platform
- Windows NTLM
- Windows Print Spooler Components
- Windows Services for NFS ONCRPC XDR Driver
- Windows Storage Spaces Controller
- Windows TCP/IP
- Windows Update
- Windows Update Assistant
- Windows User Profile Service
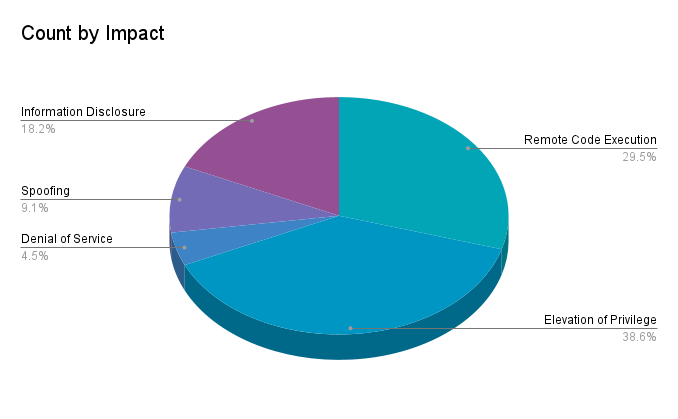
Elevation of privilege (EoP) vulnerabilities accounted for 38.6% of the vulnerabilities patched this month, followed by remote code execution (RCE) vulnerabilities at 29.5%.
CVE-2021-26424 | Windows TCP/IP Remote Code Execution Vulnerability
CVE-2021-26424 is an RCE vulnerability in the Windows implementation of TCP/IP. It received a CVSSv3 score of 9.9 and is more likely to be exploited according to Microsoft’s Exploitability Index. An attacker could remotely exploit this vulnerability by sending a specially crafted TCP/IP packet to a vulnerable Hyper-V host using the TCP/IP protocol stack to process packets. Despite Microsoft naming Hyper-V as the attack vector for this vulnerability, it has issued patches for products that do not use Hyper-V. This may indicate wider impact.
Microsoft patched two similar TCP/IP RCEs in February. CVE-2021-24074 and CVE-2021-24094 both received CVSSv3 scores of 9.8 and were labeled “Exploitation More Likely.” However, in a blog post, Microsoft indicated that exploits would be difficult to develop for these vulnerabilities. They’ve provided no additional context for CVE-2021-2624.
CVE-2021-34535 | Remote Desktop Client Remote Code Execution Vulnerability
CVE-2021-34535 is an RCE vulnerability in the Remote Desktop Client. The flaw has received a CVSSv3 score of 8.8 and is considered to be more likely to be exploited. According to the advisory, exploitation is possible in at least two scenarios. One scenario involves a victim making a remote desktop connection to an attacker-controlled server — the attacker could achieve RCE once the victim makes an initial connection with an affected version of the Remote Desktop Client. In the other scenario, a guest virtual machine (VM) on a Hyper-V server could achieve “guest-to-host RCE” after a victim on the Hyper-V host makes a connection to a malicious VM. As this vulnerability lies within the Remote Desktop Client and is not a server-side flaw, this bug is not likely wormable in an attack scenario.
CVE-2021-36936 and CVE-2021-36947 | Windows Print Spooler Remote Code Execution Vulnerability
CVE-2021-36936 and CVE-2021-36947 are RCE vulnerabilities in Windows Print Spooler. Over the past few months, Print Spooler bugs have received significant attention, starting with CVE-2021-1675 in June, followed by an out-of-band patch for CVE-2021-34527 (also known as PrintNightmare) in July.
Microsoft rates both CVE-2021-36936 and CVE-2021-36947 as “Exploitation More Likely.” CVE-2021-36936 is one of two vulnerabilities this month that Microsoft says were publicly disclosed, which may be related to several bugs in Print Spooler that were identified by researchers over the past few months.
In addition to these patches, Microsoft has also introduced significant changes to the default Point and Print behavior, more information is available in this knowledge base article. Because of the ubiquity of Windows Print Spooler, we strongly encourage organizations to apply these patches as soon as possible.
CVE-2021-36948 | Windows Update Medic Service Elevation of Privilege Vulnerability
CVE-2021-36948 is an EoP vulnerability in the Windows Update Medic Service (WaaSMedicSVC.exe). It received a CVSSv3 score of 7.8. The Windows Update Medic Service was introduced in Windows 10 to address damaged or corrupted components from the Windows Update process to ensure future Windows Updates can be received. This vulnerability was reported internally by Microsoft’s Security Response Center and Microsoft’s Threat Intelligence Center. It is the only vulnerability exploited in the wild as a zero-day this month. While RCE vulnerabilities are often the most damaging, EoP vulnerabilities are quite valuable for attackers, especially in post-compromise situations when they are looking to elevate privileges on the compromised system.
CVE-2021-36942 | Windows LSA Spoofing Vulnerability
CVE-2021-36942 is a spoofing vulnerability in Windows Local Security Authority (LSA) which could allow an unauthenticated attacker using New Technology LAN Manager (NTLM) to trick a domain controller into authenticating with another server. Microsoft encourages prioritizing patching domain controllers first and notes that further action, found in KB5005413, is required after applying the security update. While this vulnerability on its own received a CVSSv3 score of 7.5, Microsoft makes special mention that when combined with an NTLM Relay Attack, the combined score is a 9.8. Along with the update, ADV210003 is also available to provide additional guidance on “Mitigating NTLM Relay Attacks on Active Directory Certificate Services (AD CS)” in light of the recent PetitPotam NTLM Relay Attacks.
Tenable Solutions
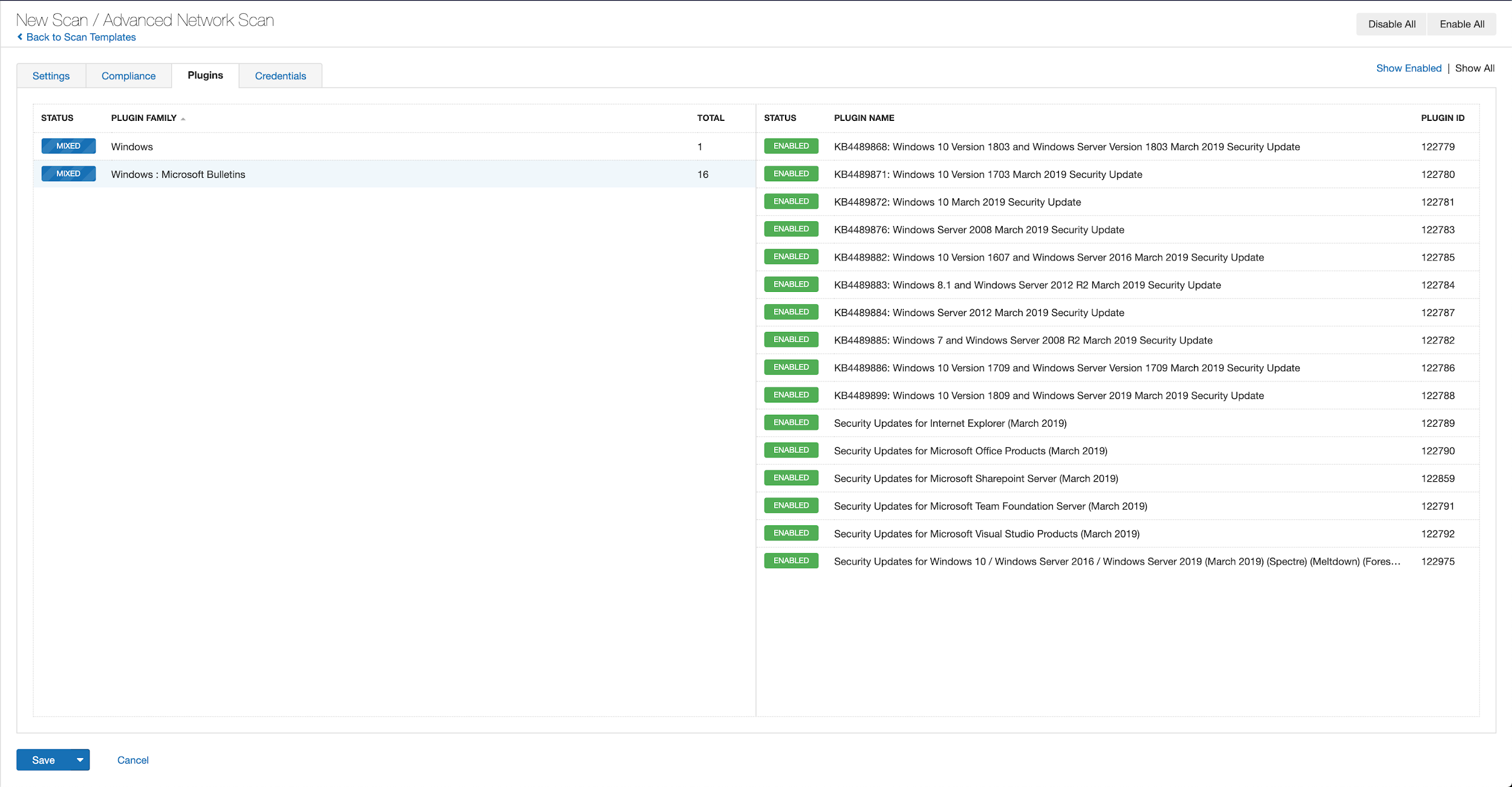
Users can create scans that focus specifically on our Patch Tuesday plugins. From a new advanced scan, in the plugins tab, set an advanced filter for Plugin Name contains August 2021.
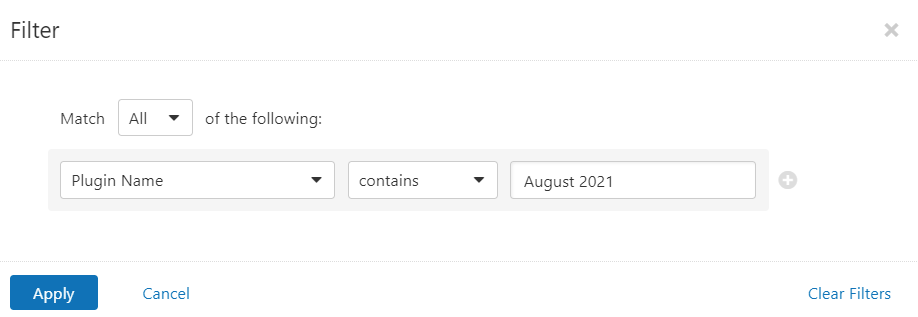
With that filter set, click the plugin families to the left and enable each plugin that appears on the right side. Note: If your families on the left say Enabled, then all the plugins in that family are set. Disable the whole family before selecting the individual plugins for this scan. Here’s an example from Tenable.io:
A list of all the plugins released for Tenable’s August 2021 Patch Tuesday update can be found here. As always, we recommend patching systems as soon as possible and regularly scanning your environment to identify those systems yet to be patched.
Get more information
- Microsoft's August 2021 Security Updates
- Tenable plugins for Microsoft August 2021 Patch Tuesday Security Updates
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.




