CVE-2019-12815: ProFTPD 中的访问控制不当漏洞被公开
Popular open source FTP daemon affected by an improper access control vulnerability dating back to 2010
背景
On July 18, Tobias Mädel published an advisory for an improper access control vulnerability in a default module for ProFTPD, a popular open source FTP daemon for Unix and Unix-like operating systems.
分析
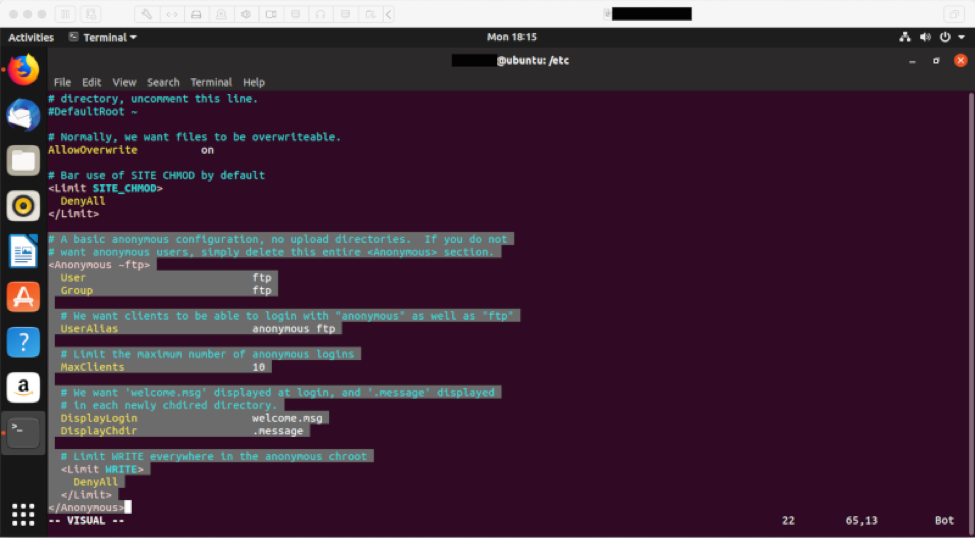
CVE-2019-12815 is an arbitrary file copy vulnerability in ProFTPD’s mod_copy module due to improper access control. According to the ProFTPD bug report for this vulnerability, mod_copy does not honor the “<Limit READ>” and “<Limit WRITE>” configuration settings in proftpd.conf, thereby allowing a remote attacker without write permissions to “copy any file on the FTP server” using CPFR and CPTO commands. This is possible under the following scenarios:
- The Anonymous user configuration is enabled on the vulnerable ProFTPD installation
- An attacker has working FTP credentials regardless of restrictions placed on the account
The former scenario is significant because it could allow a remote attacker to upload malicious files to a vulnerable server. Tenable has confirmed that anonymous user access is disabled by default when using Advanced Package Tool (APT) or Yellowdog Updater, Modified (YUM) package managers to install proftpd. However, anonymous user access is enabled by default from a source install from proftpd.org.
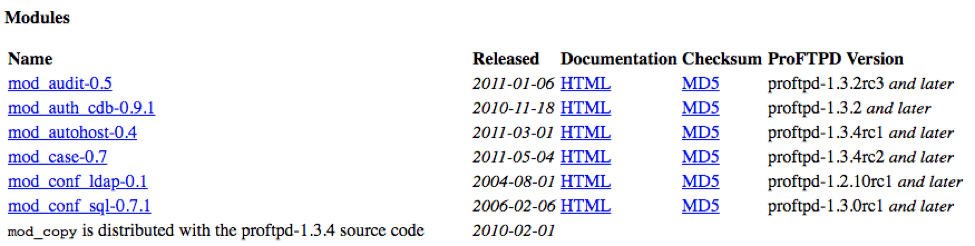
The vulnerability affects ProFTPD beginning with version 1.3.4. This is because the mod_copy module was not included as part of the default installation of ProFTPD until version 1.3.4, which was released in 2010.
In a July 23 update to his original advisory, Mädel states “Contrary to news reports, ProFTPd 1.3.6 is also affected and does not contain the fix. There is no patched release version available yet.”
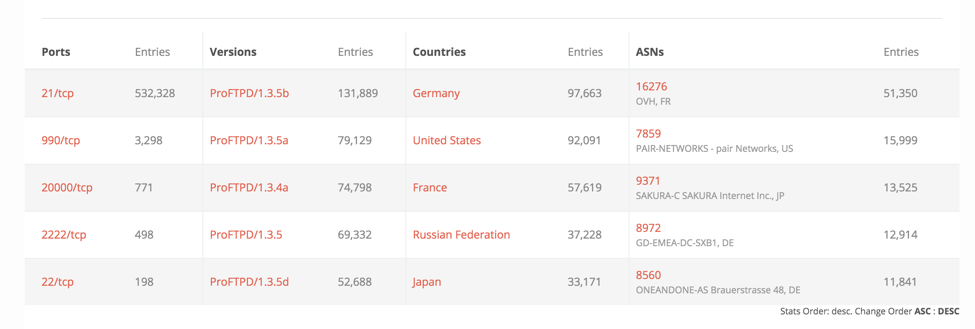
Using an internet-connected search engine, like BinaryEdge, we believe that number is close to over 539,000 potentially exposed based on the affected versions greater than 1.3.4 up to and including 1.3.6. This search does not account for whether or not these systems have anonymous user access enabled.
According to Mädel’s disclosure timeline, he reported the vulnerability to ProFTPD’s security email alias on September 28, 2018, and subsequently reported it to the Debian Security Team on June 12, 2019. Mädel provided a deadline of July 28, 2019, for public disclosure. ProFTPD released a fix to address the vulnerability on July 17, 2019.
A similar vulnerability in mod_copy, CVE-2015-3306, was disclosed in 2015, though it could be exploited by an unauthenticated attacker, making it far more severe than CVE-2019-12815.
概念验证
No Proof-of-Concept code or exploit scripts were available at the time this blog was written. However, the vulnerability details are available in the ProFTPD bug report and simply require an attacker to be able to issue CPFR and CPTO commands either as an anonymous user (if enabled) or post-authentication.
解决方案
According to the ProFTPD bug report, the fix for this vulnerability was merged in on July 17, 2019, and backported to the 1.3.6 branch. Various security trackers for Debian, Ubuntu and other Linux or Unix distributions show they remain unpatched and vulnerable. SUSE is not affected by this vulnerability. However, Mädel’s July 23 update to his advisory states that the vulnerability was not fixed in 1.3.6.
Until the patch is released and available downstream, users can disable mod_copy in the ProFTPD configuration file as a workaround.
识别受影响的系统
A list of Tenable plugins to identify this vulnerability will appear here as they’re released. Additionally, there are Tenable plugins to identify when Anonymous FTP access is enabled.
获取更多信息
- Tobias Mädel's Advisory for CVE-2019-12815
- ProFTPD Bug Tracker: CVE-2019-12815
- ProFTPD Bug Tracker: CVE-2015-3306
加入 Tenable Community 中的 Tenable 安全响应团队
了解有关 Tenable 这款首创 Cyber Exposure 平台的更多信息,全面管理现代攻击面。
Get a free 60-day trial of Tenable.io.
相关文章
- Threat Intelligence
- Threat Management
- Vulnerability Management
- Vulnerability Scanning






