網路安全快照: Are SBOMs on Your Supply Chain Security Radar Screen? Check Out New Recommendations from CISA and NSA

The SBOM concept is still half-baked, but CISA and NSA want to help change that with new best practices for software vendors, developers and buyers. Plus, there’s new guidance about the Royal ransomware gang – as ransomware attacks grow. In addition, Google highlights a new typosquatting trend impacting cloud storage. 更多内容不一一列举!
Dive into six things that are top of mind for the week ending November 17.
1 - CISA, NSA push SBOM adoption to beef up supply chain security
As the Log4Shell bug and SolarWinds hack made clear, cybersecurity teams must continuously assess and mitigate risks in their organizations’ software supply chain. A key tool to do that, experts say, is the software bill of materials (SBOM).
原因是什么?Conceptually, an SBOM is a list of all components in a software product. Thus, when a critical vulnerability in a software building block is disclosed – such as Log4Shell in Log4j – SBOMs should help cyber teams locate instances of the vulnerability in their environment.

However, SBOMs remain a work in progress. There’s no consensus on standard formats; on the information they should contain; nor on the best way to use them. Nonetheless, software buyers in the public and private sectors alike are increasingly requiring SBOMs from software vendors.
To help move SBOMs forward, the Cybersecurity and Infrastructure Security Agency (CISA) and the National Security Agency (NSA) have just released the guide “Securing the Software Supply Chain: Recommended Practices for Software Bill of Materials Consumption.”
The guide acknowledges that SBOM consumption is “new and will evolve and scale” and that “emerging tools” will help automate it. “Until recently, SBOM data was quite scarce, so there wasn’t much need for open source software or proprietary SBOM consumption tools,” reads the guide.
The 32-page document offers best practices and principles for software developers and suppliers. It can also be used by software buyers to assess their supply chain security practices. 文章主题涵盖:
- Operationalizing and scaling SBOM use
- Ingesting and managing SBOMs by enterprises
- Turning SBOMs into risk information
To get more details, check out the joint alert from CISA and the NSA and the full guide “Securing the Software Supply Chain: Recommended Practices for Software Bill of Materials Consumption.”
For more information about the status of SBOM standards and adoption:
- “Software bills of material face long road to adoption” (FedScoop)
- “What is a software bill of materials (SBOM)? And will it secure supply chains?” (SDX Central)
- “How to create an SBOM, with example and template” (TechTarget)
- “SBOMs – Software Supply Chain Security’s Future or Fantasy?” (SecurityWeek)
- “SBOMs and security: What IT and DevOps need to know” (TechTarget)
VIDEOS
An SBOM Primer: From Licenses to Security, Know What’s in Your Code (Linux Foundation)
SBOM Explainer: What Is SBOM? Part 1 (NTIA)
2 - Royal ransomware advisory gets updated with new IOCs, TTPs
A U.S. government advisory on the Royal ransomware group has just gotten updated after its initial release in March of this year.
The revamped version of the “#StopRansomware: Royal Ransomware” advisory, published this week, adds information on tactics, techniques and procedures (TTPs), as well as on indicators of compromise (IOCs).
To date, Royal has victimized 350-plus organizations globally, using primarily phishing emails as its preferred vector for initial access. The group’s ransom demands now exceed $275 million. And apparently the group is planning a makeover.

“There are indications that Royal may be preparing for a re-branding effort and/or a spinoff variant,” reads the updated advisory, published by CISA and the FBI.
To get all the details, read the 14-page advisory.
For more information about recent ransomware trends and incidents:
- “Ransomware Attacks Are on the Rise, Again” (Wired)
- “Healthcare giant McLaren reveals data on 2.2 million patients stolen during ransomware attack” (TechCrunch)
- “Weeks after Boeing attack, ransomware group leaks allegedly stolen files” (Cybersecurity Dive)
- “MOVEit Hackers Pivot to SysAid Zero-Day in Ransomware Attacks” (Dark Reading)
- “Meet Rhysida, a New Ransomware Strain That Deletes Itself” (Dark Reading)
VIDEOS
Tenable CEO Amit Yoran 与 CNN 讨论拉斯维加斯勒索软件攻击
Tenable 网络观察:美国Gov Updates Ransomware Guide
Tenable.ot Security Spotlight - Episode 1: The Ransomware Ecosystem
3 - Report: New ransomware gangs drove up attacks in September
Ransomware attacks ramped up in September, boosted by recently formed ransomware groups like LostTrust and RansomedVC.
That’s according to the latest “Monthly Threat Pulse” report by NCC Group, which observed a 32% spike in attacks compared with August of this year, and of 153% compared with September of 2022. The number of attacks observed in September is the highest ever recorded by NCC Group.
LostTrust ranked second among the most active ransomware gangs, accounting for 10% of all September attacks, while RansomedVC came in fourth with 9%.
“The influx of new groups is evidence of the evolving nature of global ransomware attacks. There’s a focus on ramping up pressure on victims,” Matt Hull, Global Head of Threat Intelligence at NCC Group, said in a statement.
Top 10 Most Active Ransomware Groups in September 2023
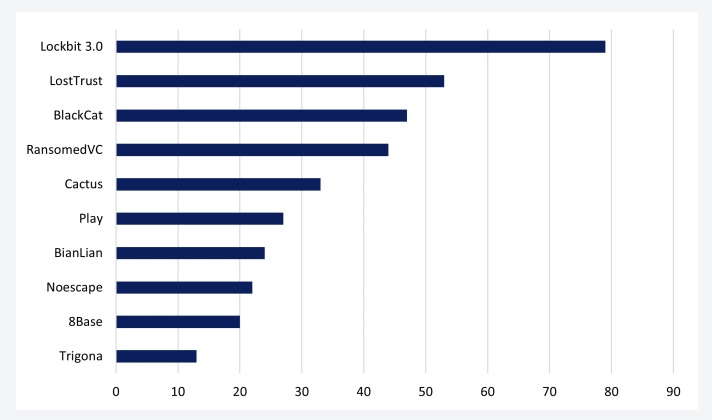
(Source: NCC Group’s Cyber Threat Intelligence Report, September 2023)
The hardest-hit vertical industries were industrials, consumer cyclicals, technology and healthcare.
To get more details, read the report’s announcement “New threat actors drive record levels of ransomware attacks in September” and the full report “NCC Group: Cyber Threat Intelligence Report, September 2023.”
4 - Where are you on your identity zero-trust journey?
During our recent webinar “Tenable Identity Exposure Customer Update: November 2023,” we polled participants on various zero-trust topics related to identity security. Check out what respondents said when we asked them if their organization has a zero-trust program and to rate their identity zero-trust levels.
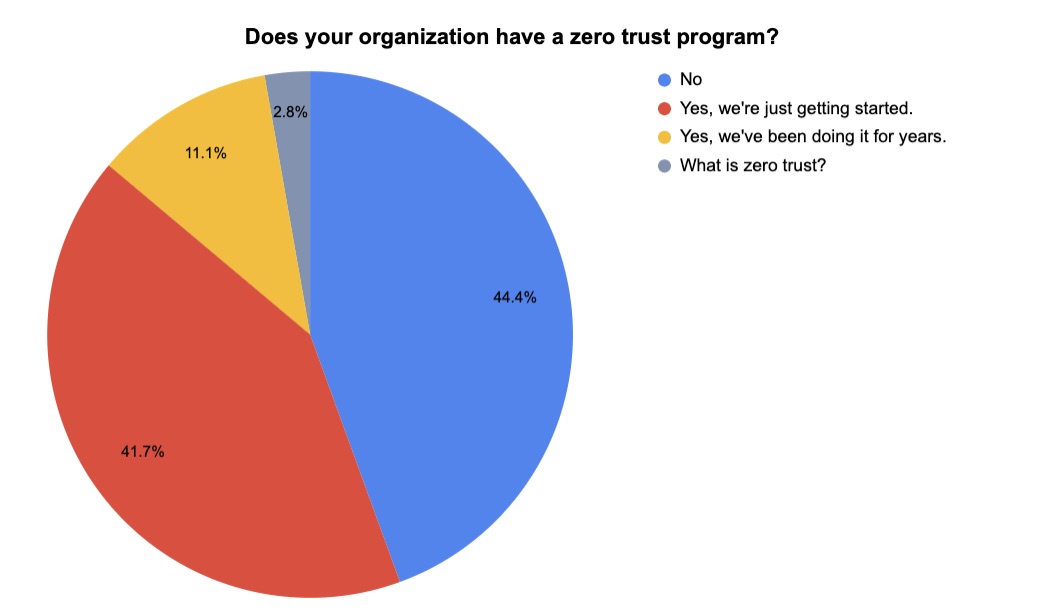
(36 respondents polled by Tenable in October 2023)
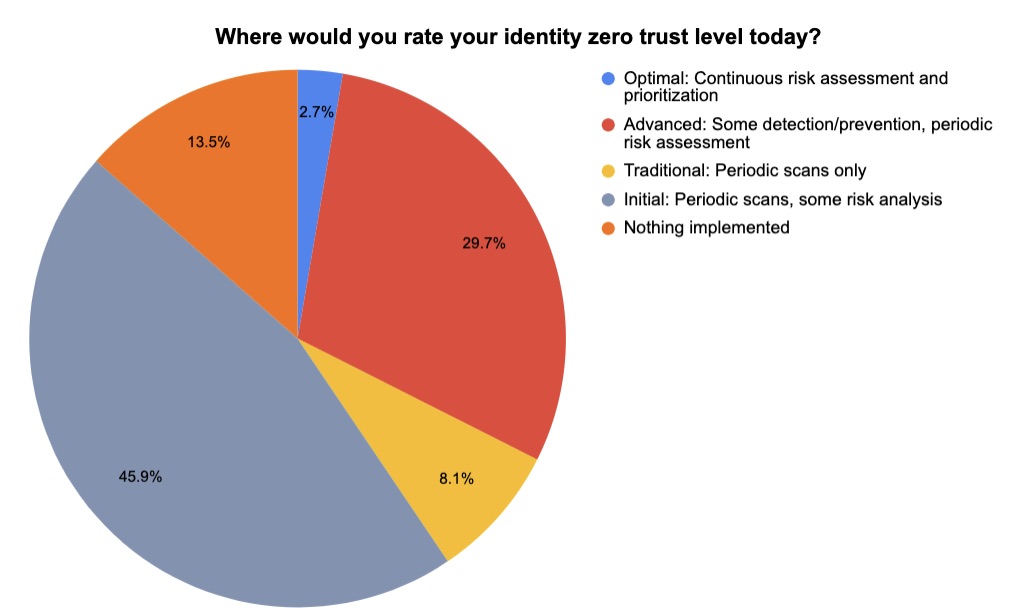
(37 respondents polled by Tenable in October 2023)
To get all the details from the “Tenable Identity Exposure Customer Update: November 2023” webinar, watch it on demand!
5 - Google highlights cloud typosquatting threat in new report
Is your cloud security team keeping tabs on typosquatting threats? In these attacks, cyber crooks set up malicious websites whose URLs are misspelled variations of legitimate domains. A new Google report addresses an interesting angle of this threat.
Specifically, the “Q3 2023 Threat Horizons Report” from Google’s Cybersecurity Action Team covers a trend where hackers target cloud storage platforms with typosquatting. When users mistakenly mistype these storage services’ URLs and inadvertently land on malicious sites, attackers try to steal their data and login credentials, as well as infect their devices.
Examples of typosquatted domains
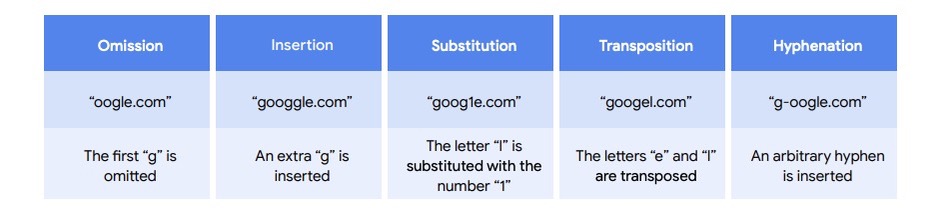
(Source: “Q3 2023 Threat Horizons Report,” Google’s Cybersecurity Action Team, November 2023)
Google’s recommended mitigations include:
- Understand to what degree your organizations’ domain has been typosquatted
- Report cloud storage typosquatting domains to the appropriate cloud provider, such as Google, Amazon or Microsoft
- Proactively register domain variations
The report also covers other topics, including cloud compromise methods observed in Q2; threats against data stored in software-as-a-service systems; and potential abuses of Google Calendar.
To get more details, read the “Q3 2023 Threat Horizons Report” from Google’s Cybersecurity Action Team.
6 - OMB drafts guidance for fed agencies’ AI use
Are you involved with drafting your organization’s policy for the use of artificial intelligence? You might want to take a peek at how the U.S. government is going about this task. The Office of Management and Budget (OMB) recently issued a draft memo for ensuring that federal agencies’ AI use is secure, legal and innovative.

The 26-page draft memorandum, titled “Advancing Governance, Innovation, and Risk Management for Agency Use of Artificial Intelligence,” focuses on establishing requirements and guidance in three main areas:
- Strengthening AI governance, including the requirement that each agency appoint a Chief AI Officer (CAIO)
- Advancing responsible AI innovation, including the requirement that certain agencies outline an enterprise AI strategy
- Managing risks from the use of AI, especially when it will impact the rights and safety of citizens
To get more details, read the memo.
For more information about AI usage policies and governance best practices:
- “Key Considerations for Developing Organizational Generative AI Policies” (ISACA)
- “Establishing governance for AI systems” (IAPP)
- “What is artificial intelligence (AI) governance?” (TechTarget)
- “CISOs push for baseline AI business rules” (SC Magazine)
- “AI policies should start with the basics, legal chiefs say” (Legal Dive)
VIDEOS
Responsible AI: Tackling Tech's Largest Corporate Governance Challenges (University of California Berkeley)
Governance and the Future of AI (Center for Strategic & International Studies)
相关文章
- Cloud
- Exposure Management
- Vulnerability Management
- Cloud
- Cybersecurity Snapshot
- Exposure Management
- Federal
- Government
- Malware
- Vulnerability Management





